diff --git a/.gitignore b/.gitignore
index 05d67e1..21388f4 100644
--- a/.gitignore
+++ b/.gitignore
@@ -2,14 +2,16 @@
*.o
*.swp
*_temp/
-*logs/
+*.log
*.log
*.pid
*.out
*.rdb
t/servroot/
*temp/
-*.sh
+*.pyc
-*stdout
+*stdout*
+stdout
+*.log
diff --git a/LICENSE b/LICENSE
index d5802f8..2720490 100644
--- a/LICENSE
+++ b/LICENSE
@@ -1,6 +1,6 @@
The MIT License (MIT)
-Copyright (c) 2015 渣浪研发中心技术保障部移动端保障团队
+Copyright (c) 2016 CNSRE 技术保障团队
Permission is hereby granted, free of charge, to any person obtaining a copy
of this software and associated documentation files (the "Software"), to deal
diff --git a/README.md b/README.md
index af934da..c416fa0 100644
--- a/README.md
+++ b/README.md
@@ -1,32 +1,25 @@
-基于动态策略的灰度发布系统
-========================
-ABTestingGateway 是一个可以动态设置分流策略的灰度发布系统,工作在7层,基于[nginx](http://nginx.org/)和[ngx-lua](https://github.com/openresty/lua-nginx-module)开发,使用 redis 作为分流策略数据库,可以实现动态调度功能。
-
-nginx是目前使用较多的7层服务器,可以实现高性能的转发和响应;ABTestingGateway 是在 nginx 转发的框架内,在转向 upstream 前,根据 用户请求特征 和 系统的分流策略 ,查找出目标upstream,进而实现分流。
-
-在以往的基于 nginx 实现的灰度系统中,分流逻辑往往通过 rewrite 阶段的 if 和 rewrite 指令等实现,优点是`性能较高`,缺点是`功能受限`、`容易出错`,以及`转发规则固定,只能静态分流`。针对这些缺点,我们设计实现了ABTestingGateway,采用 ngx-lua 实现系统功能,通过启用[lua-shared-dict](http://wiki.nginx.org/HttpLuaModule#ngx.shared.DICT)和[lua-resty-lock](https://github.com/openresty/lua-resty-lock)作为系统缓存和缓存锁,系统获得了较为接近原生nginx转发的性能。
-
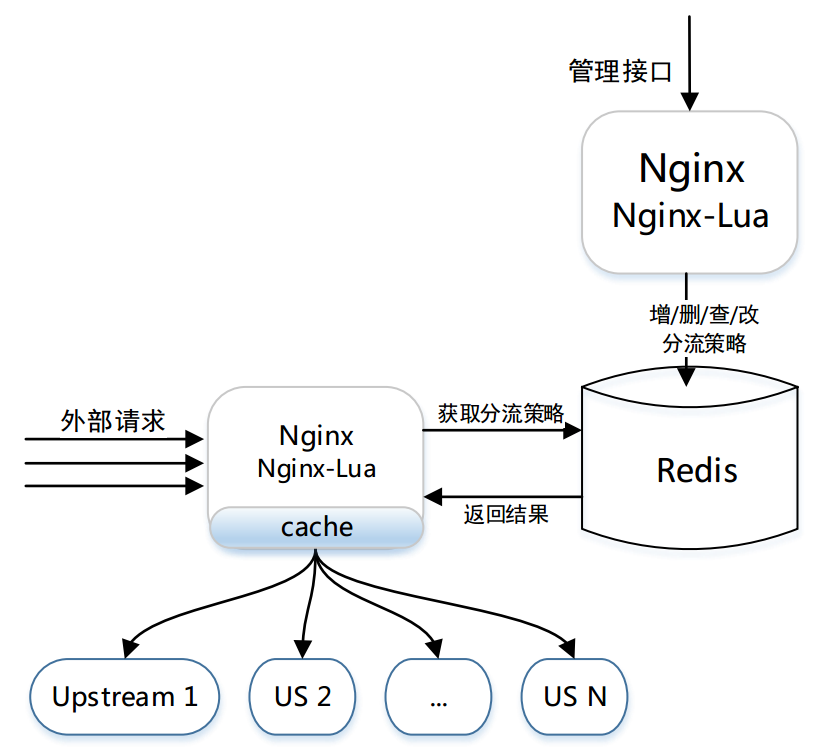
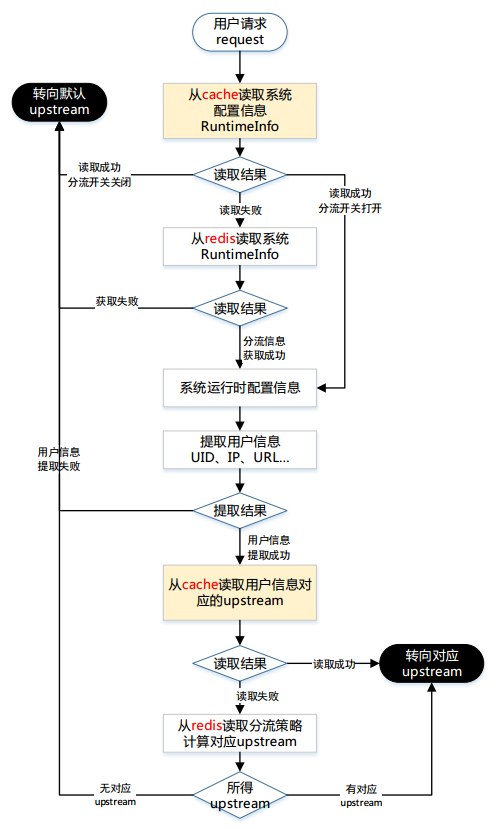
ABTestingGateway 的架构简图
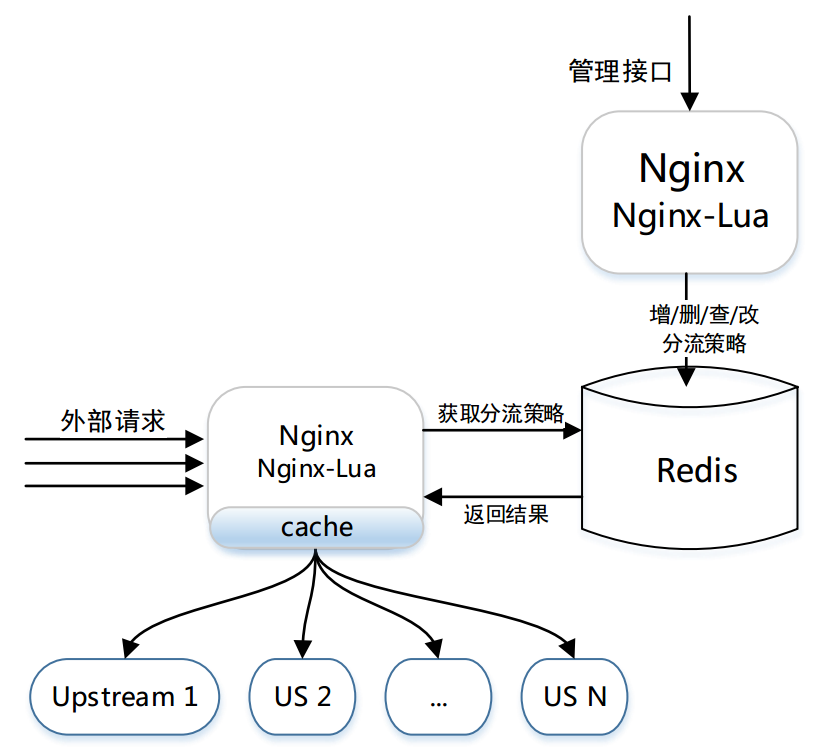
ABTestingGateway 的架构简图
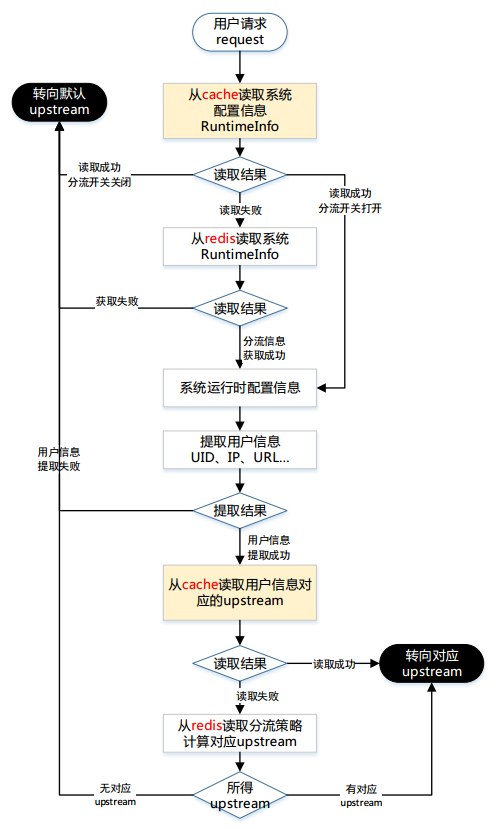
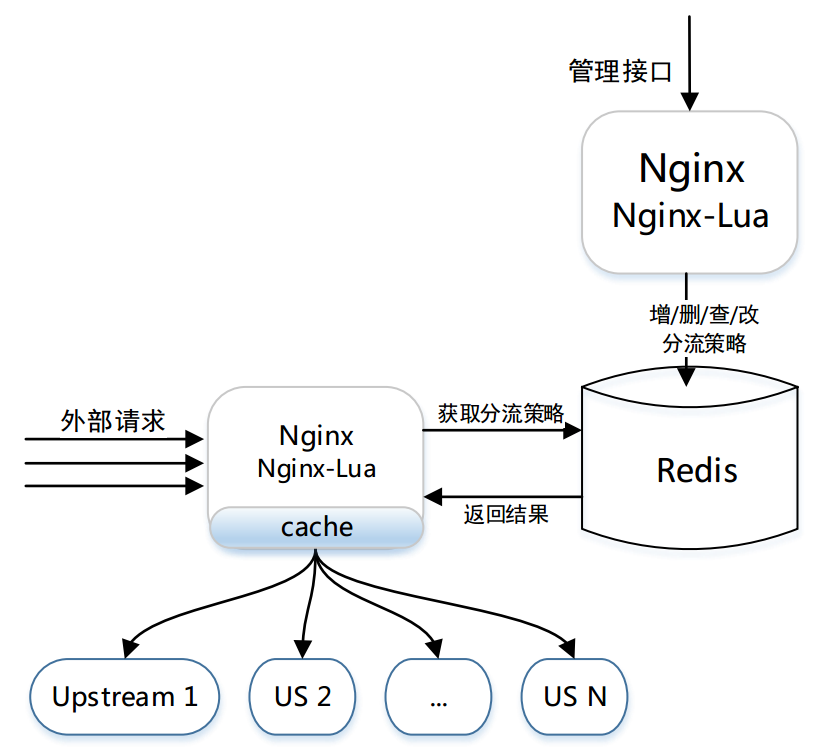
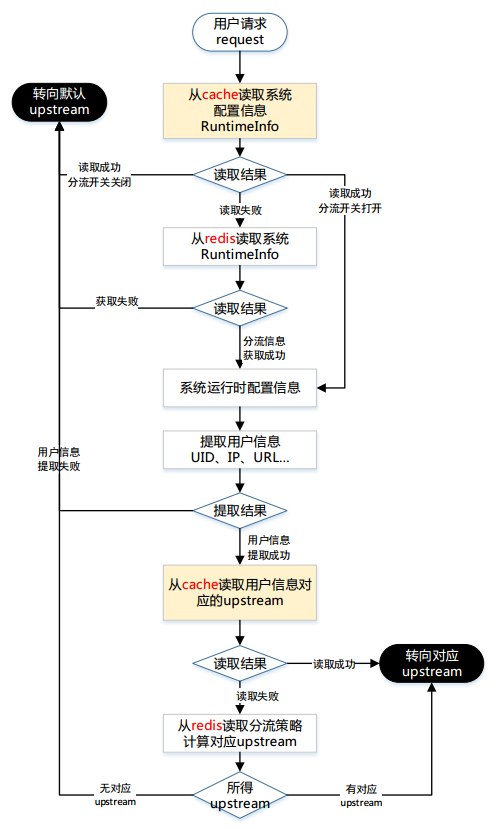
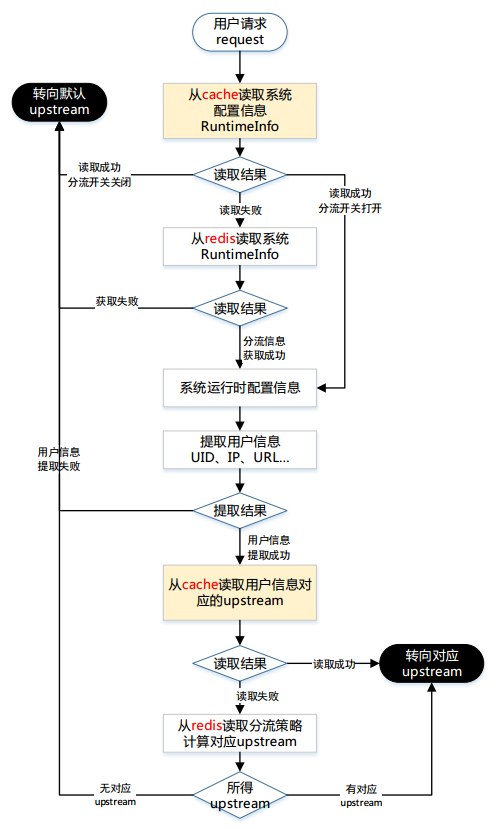
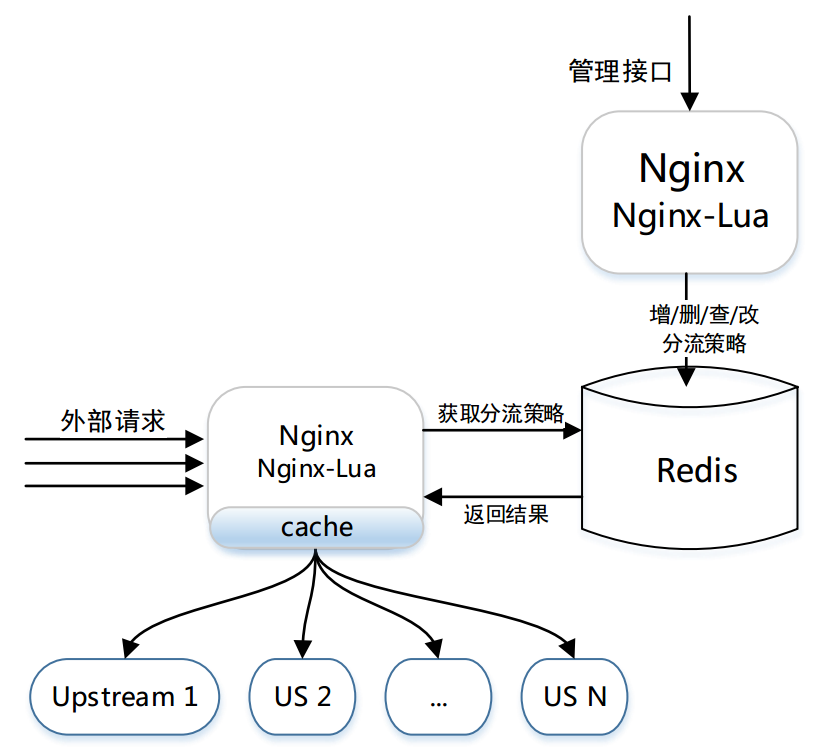
分流过程流程图
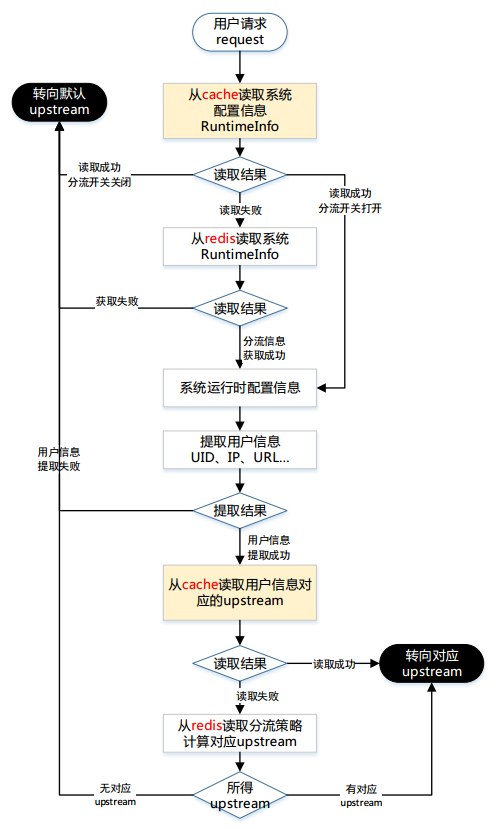
分流过程流程图
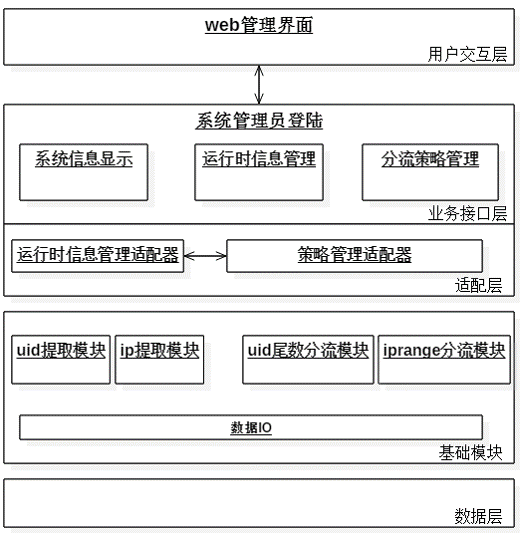
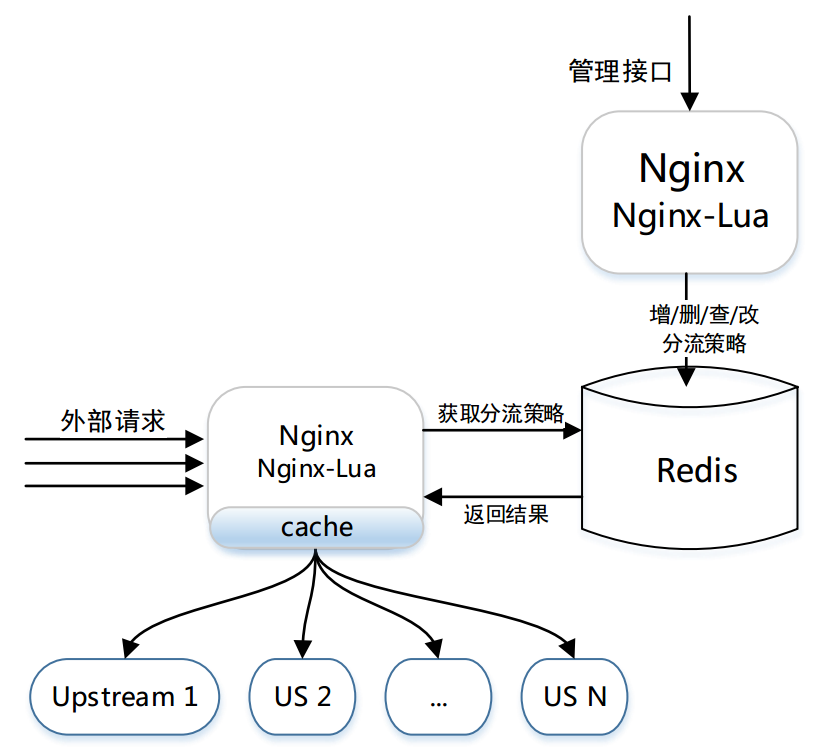
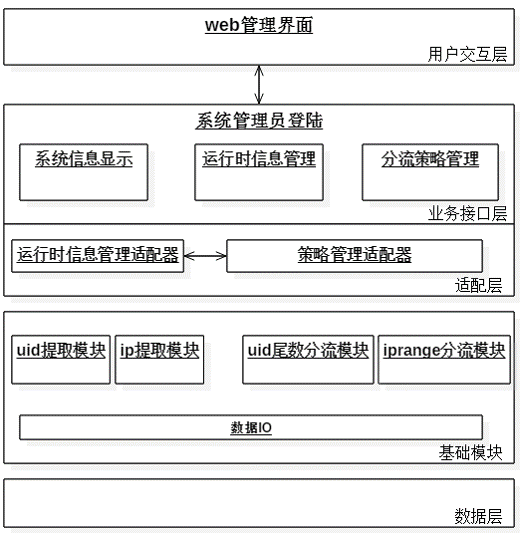
管理功能架构图
-[策略管理接口]
- #分流策略检查,参数为一个分流策略数据的json串
- 1. /admin/policy/check
- #分流策略添加,参数与check接口一致
- 2. /admin/policy/set
- #分流策略读取,参数为要读取策略的policyid
- 3. /admin/policy/get
- #分流策略删除,参数为要删除策略的policyid
- 4. /admin/policy/del
-
-[运行时信息管理接口]
- #设置分流策略为运行时策略,参数为policyid
- 1. /admin/runtime/set
- #获取系统当前运行时信息,无参数
- 2. /admin/runtime/get
- #删除系统运行时信息,关闭分流接口,无参数
- 3. /admin/runtime/del
-
-
-快速部署
-----------
+系统部署
+=========================
+
+软件依赖
+------------------
-###软件依赖
-- tengine-2.1.0
-- LuaJIT-2.1-20141128
-- ngx_lua-0.9.13
-- lua-cjson-2.1.0.2
-- redis-2.8.19
+* openresty
+* ngx_lua
+* LuaJIT
+* lua-cjson
+* redis
+> > 注意:建议选用openresty最新版,但是从openresty-1.9.15.1开始,lua-resty-core有些api变更,因此建议先使用openresty-1.9.7.5,原因是:[必读](https://github.com/CNSRE/ABTestingGateway/issues/27#issuecomment-236149255)
-###系统部署
+> > 注意:tengine用户仍然可以使用本项目,只需要从openresty软件包中获取最新的ngx_lua、LuaJIT以及lua-cjson等,并注意:[必读](https://github.com/CNSRE/ABTestingGateway/issues/27#issuecomment-236149255)
+
+how to start
+-----------------------
repo中的`utils/conf`文件夹中有灰度系统部署所需的最小示例
-
+> 目前repo的master分支是支持多级分流的版本,如果只想体验单级分流,可以fork single_diversion_release分支,具体文档都在相关分支的readme中。
+
+```bash
1. git clone https://github.com/SinaMSRE/ABTestingGateway
-2. cd /path/to/ABTestingGateway/utils
+2. cd /path/to/ABTestingGateway/utils && mkdir logs
-#启动redis数据库
+# 启动redis数据库
3. redis-server conf/redis.conf
-#启动upstream server,其中stable为默认upstream
+# 启动upstream server,其中stable为默认upstream
4. /usr/local/nginx/sbin/nginx -p `pwd` -c conf/stable.conf
5. /usr/local/nginx/sbin/nginx -p `pwd` -c conf/beta1.conf
6. /usr/local/nginx/sbin/nginx -p `pwd` -c conf/beta2.conf
7. /usr/local/nginx/sbin/nginx -p `pwd` -c conf/beta3.conf
8. /usr/local/nginx/sbin/nginx -p `pwd` -c conf/beta4.conf
-#启动灰度系统,proxy server,灰度系统的配置也写在conf/nginx.conf中
+# 启动灰度系统,proxy server,灰度系统的配置也写在conf/nginx.conf中
9. /usr/local/nginx/sbin/nginx -p `pwd` -c conf/nginx.conf
-
-
-###灰度系统使用demo
---------------
-1. 管理功能
-
- 1. 部署并启动系统
-
- 2. 查询系统运行时信息,得到null
- 0> curl 127.0.0.1:8030/admin/runtime/get
- {"errcode":200,"errinfo":"success ","data":{"divModulename":null,"divDataKey":null,"userInfoModulename":null}}
-
- 3. 查询id为9的策略,得到null
- 0> curl 127.0.0.1:8030/admin/policy/get?policyid=9
- {"errcode":200,"errinfo":"success ","data":{"divdata":null,"divtype":null}}
-
- 4. 向系统添加策略,返回成功,并返回新添加策略的policyid
- 以uidsuffix尾数分流方式为例,示例分流策略为:
- {
- "divtype":"uidsuffix",
- "divdata":[
- {"suffix":"1", "upstream":"beta1"},
- {"suffix":"3", "upstream":"beta2"},
- {"suffix":"5", "upstream":"beta1"},
- {"suffix":"0", "upstream":"beta3"}
- ]
- }
- 添加分流策略接口 /admin/policy/set 接受json化的policy数据
- 0> curl 127.0.0.1:8030/admin/policy/set -d '{"divtype":"uidsuffix","divdata":[{"suffix":"1","upstream":"beta1"},{"suffix":"3","upstream":"beta2"},{"suffix":"5","upstream":"beta1"},{"suffix":"0","upstream":"beta3"}]}'
- {"errcode":200,"errinfo":"success the id of new policy is 0"}
-
- 5. 查看添加结果
- 0> curl 127.0.0.1:8030/admin/policy/get?policyid=0
- {"errcode":200,"errinfo":"success ","data":{"divdata":["1","beta1","3","beta2","5","beta1","0","beta3"],"divtype":"uidsuffix"}}
-
- 6. 设置系统运行时策略为 0号策略
- 0> curl 127.0.0.1:8030/admin/runtime/set?policyid=0
- {"errcode":200,"errinfo":"success "}
-
- 7. 查看系统运行时信息,得到结果
- 0> curl 127.0.0.1:8030/admin/runtime/get
- {"errcode":200,"errinfo":"success ","data":{"divModulename":"abtesting.diversion.uidsuffix","divDataKey":"ab:test:policies:0:divdata","userInfoModulename":"abtesting.userinfo.uidParser"}}
-
- 8. 当访问接口不正确返回时,将返回相应的 错误码 和 错误描述信息
- 0> curl 127.0.0.1:8030/admin/policy/get?policyid=abc
- {"errcode":50104,"errinfo":"parameter type error for policyID should be a positive Integer"}
-
-
-2. 分流功能
-
- 在验证管理功能通过,并设置系统运行时策略后,开始验证分流功能
-
- 1. 分流,不带用户uid,转发至默认upstream
- 0> curl 127.0.0.1:8030/
- this is stable server
-
- 2. 分流,带uid为30,根据策略,转发至beta3
- 0> curl 127.0.0.1:8030/ -H 'X-Uid:30'
- this is beta3 server
-
- 3. 分流,带uid为33,根据策略,转发至beta2
- 0> curl 127.0.0.1:8030/ -H 'X-Uid:33'
- this is beta2 server
+
+# 简单验证:添加分流策略组
+$ curl 127.0.0.1:8080/ab_admin?action=policygroup_set -d '{"1":{"divtype":"uidsuffix","divdata":[{"suffix":"1","upstream":"beta1"},{"suffix":"3","upstream":"beta2"},{"suffix":"5","upstream":"beta1"},{"suffix":"0","upstream":"beta3"}]},"2":{"divtype":"arg_city","divdata":[{"city":"BJ","upstream":"beta1"},{"city":"SH","upstream":"beta2"},{"city":"XA","upstream":"beta1"},{"city":"HZ","upstream":"beta3"}]},"3":{"divtype":"iprange","divdata":[{"range":{"start":1111,"end":2222},"upstream":"beta1"},{"range":{"start":3333,"end":4444},"upstream":"beta2"},{"range":{"start":7777,"end":2130706433},"upstream":"beta2"}]}}'
+
+{"desc":"success ","code":200,"data":{"groupid":0,"group":[0,1,2]}}
+
+# 简单验证:设置运行时策略
+
+$ curl "127.0.0.1:8080/ab_admin?action=runtime_set&hostname=api.weibo.cn&policygroupid=0"
+
+# 分流
+$ curl 127.0.0.1:8030 -H 'X-Uid:39' -H 'X-Real-IP:192.168.1.1'
+this is stable server
+
+$ curl 127.0.0.1:8030 -H 'X-Uid:30' -H 'X-Real-IP:192.168.1.1'
+this is beta3 server
+
+$ curl 127.0.0.1:8030/?city=BJ -H 'X-Uid:39' -H 'X-Real-IP:192.168.1.1'
+this is beta1 server
+
+```
+
+配置过程
+------------------------
+
+* 由于内部部署时以dygateway项目名部署,因此下文中的所有配置,都应将ABTestingGateway文件夹重命名为dygateway
+
+[nginx.conf配置过程](doc/nginx_conf_配置过程.md)
+
+[redis.conf配置过程](doc/redis_conf_配置过程.md)
+
+
+系统使用
+=========================
+
+ab分流策略
+-----------------
+
+* ab功能目前支持的分流策略有
+ * iprange: ip段分流
+ * uidrange: 用户uid段分流
+ * uidsuffix: uid尾数分流
+ * uidappoint: uid白名单分流
+
+* 可以灵活添加新的分流方式
+
+[ab分流策略格式和样例](doc/ab分流策略.md)
+
+ab功能接口
+------------------
+
+* [ab功能接口说明文档](doc/ab功能接口使用介绍.md)
+
+```bash
+ * 策略管理:增删改查
+ /ab_admin?action=policy_check
+ /ab_admin?action=policy_set
+ /ab_admin?action=policy_get
+ /ab_admin?action=policy_del
+
+ * 策略组管理(用于多级分流)
+ /ab_admin?action=policygroup_check
+ /ab_admin?action=policygroup_set
+ /ab_admin?action=policygroup_get
+ /ab_admin?action=policygroup_del
+
+ * 运行时信息管理
+ * 其中runtime_set接受policyid和policygroupid参数,分别用于单级分流和多级分流
+
+ /ab_admin?action=runtime_get
+ /ab_admin?action=runtime_set
+ /ab_admin?action=runtime_del
+```
压测结果:
-----------
@@ -213,8 +177,60 @@ proxy server的硬件配置:
- Mem:24GB
- Nic:千兆网卡,多队列,理论流量峰值为125MB/s
+* 注:压测结果是单级分流模式的压力测试结果,多级压测与单级压测的数据像差不多,因为ngx_lua的执行时间仅占ab功能的小部分,瓶颈不在于此
+
+
线上部署简图:
-----------
+FAQ
+-------------------------------
+
+* 启动时报错,[提示ngx_http_lua_ffi_semaphore_new未定义](https://github.com/CNSRE/ABTestingGateway/issues/27)
+ * 这个是ngx_lua比较新的版本中带有的 resty.semaphore模块,请确定ngx_lua版本包含该模块
+ * LuaJIT也请采用openresty软件包中提供的版本
+ * 其实直接采用openresty最好,使用最新版本的openresty不会用软件依赖问题,只是我所在的项目组有tengine的需求,所以用tengine
+* 为什么都root用户了还会提示Permission denied, [solution](https://github.com/CNSRE/ABTestingGateway/issues/28)
+
+TODO LIST
+----------------------------
+
+* 开发nginx shm storage模块,扩展 ngx-shared-dict 的功能
+ * 目前 ngx-shared-dict 提供高效快速的 kv 式简单存储
+ * 简单高效的存储,不足之处最直接的体现在不支持缓存 lua table。[lua-resty-lrucache提供LuaVM级别的缓存,不能跨worker共享]
+ * 目前团队同学基于红黑树实现了类似于ngx-shared-dict的存储功能,可以存储任意类型,查找方式由用户自定义。项目地址:[ngx-shared-rbtree](https://github.com/helloyi/ngx-lua-shrbtree-module)
+ * ngx-shared-rbtree的不足之处在于“模块只能存储一颗红黑树”,不能实现复杂用法,因此需要被进一步扩展。类似于如下所示的使用方法:
+
+```bash
+
+local dict = ngx.shared.ngxdb
+-----------------------------------
+
+local db_tab = "db_tab"
+local k_tab = {["a"]=1, ["b"]=2}
+local v_tab = {1, 2, 3}
+
+dict:set(db_tab, k_tab, v_tab)
+
+local v_tab = dict:get(db_tab, k_tab)
+-----------------------------------
+
+local db_kv = "db_kv"
+local k = "foo"
+local v = "bar"
+
+dict:set(db_kv, k, v)
+
+local getv = dict:get(db_kv, v)
+-----------------------------------
+```
+* 扩展ABTestingGateway的功能
+ * 由于该项目最初是为手机微博7层开发的,所以只关注了分流功能。
+ * 而项目在公司内部使用过程中发现,不同业务对于ab项目这层转发工作的期许不太一样
+ * 有的业务需要将用户分流到不同的服务器上
+ * 有的业务需要在这步处理中根据策略增减用户请求的uri参数或者header头
+ * 所以扩展ab项目的这层转发很有必要,目前随着在公司内部的推广,也在不停的收集需求,探索新的玩法
+ * 其实整个AB项目并没有太高的技术含量,大家关于ab和分流的玩法都大同小异,所不同的是,我们在这种范式下,能发出多少有趣的花样,期待大家多多交流
+* 逐步开源dygateway的所有功能
diff --git a/admin/ab_action.lua b/admin/ab_action.lua
new file mode 100644
index 0000000..7c85248
--- /dev/null
+++ b/admin/ab_action.lua
@@ -0,0 +1,92 @@
+local policyModule = require('abtesting.adapter.policy')
+local redisModule = require('abtesting.utils.redis')
+local systemConf = require('abtesting.utils.init')
+local handler = require('abtesting.error.handler').handler
+local utils = require('abtesting.utils.utils')
+local log = require('abtesting.utils.log')
+local ERRORINFO = require('abtesting.error.errcode').info
+local policy = require("admin.policy")
+local runtime = require('admin.runtime')
+local policygroup = require("admin.policygroup")
+
+local cjson = require('cjson.safe')
+local doresp = utils.doresp
+local dolog = utils.dolog
+
+local redisConf = systemConf.redisConf
+local divtypes = systemConf.divtypes
+local prefixConf = systemConf.prefixConf
+local policyLib = prefixConf.policyLibPrefix
+local runtimeLib = prefixConf.runtimeInfoPrefix
+local domain_name = prefixConf.domainname
+
+local ab_action = {}
+
+ab_action.policy_check = policy.check
+ab_action.policy_set = policy.set
+ab_action.policy_get = policy.get
+ab_action.policy_del = policy.del
+
+ab_action.runtime_set = runtime.set
+ab_action.runtime_del = runtime.del
+ab_action.runtime_get = runtime.get
+
+
+ab_action.policygroup_check = policygroup.check
+ab_action.policygroup_set = policygroup.set
+ab_action.policygroup_get = policygroup.get
+ab_action.policygroup_del = policygroup.del
+
+
+local get_uriargs_error = function()
+ local info = ERRORINFO.ACTION_BLANK_ERROR
+ local response = doresp(info, 'user req')
+ log:errlog(dolog(info, desc))
+ ngx.say(response)
+ return
+end
+
+local get_action_error = function()
+ local info = ERRORINFO.ACTION_BLANK_ERROR
+ local response = doresp(info, 'user req')
+ log:errlog(dolog(info, desc))
+ ngx.say(response)
+ return
+end
+
+local do_action_error = function(action)
+ local info = ERRORINFO.DOACTION_ERROR
+ local desc = action
+ local response = doresp(info, desc)
+ local errlog = dolog(info, desc)
+ log:errlog(errlog)
+ ngx.say(response)
+ return
+end
+
+local red = redisModule:new(redisConf)
+local ok, err = red:connectdb()
+if not ok then
+ local info = ERRORINFO.REDIS_CONNECT_ERROR
+ local response = doresp(info, err)
+ log:errlog(dolog(info, desc))
+ ngx.say(response)
+ return
+end
+
+local args = ngx.req.get_uri_args()
+if args then
+ local action = args.action
+ local do_action = ab_action[action]
+ if do_action then
+ do_action({['db']=red})
+-- local ok, info = do_action(policy, {['db']=red})
+-- if not ok then
+-- do_action_error()
+-- end
+ else
+ do_action_error(action)
+ end
+else
+ get_uriargs_error()
+end
diff --git a/admin/action.lua b/admin/action.lua
new file mode 100644
index 0000000..9a6d1aa
--- /dev/null
+++ b/admin/action.lua
@@ -0,0 +1,83 @@
+local policyModule = require('abtesting.adapter.policy')
+local redisModule = require('abtesting.utils.redis')
+local systemConf = require('abtesting.utils.init')
+local handler = require('abtesting.error.handler').handler
+local utils = require('abtesting.utils.utils')
+local ERRORINFO = require('abtesting.error.errcode').info
+
+local cjson = require('cjson.safe')
+local doresp = utils.doresp
+local dolog = utils.dolog
+
+local redisConf = systemConf.redisConf
+local divtypes = systemConf.divtypes
+local prefixConf = systemConf.prefixConf
+local policyLib = prefixConf.policyLibPrefix
+local runtimeLib = prefixConf.runtimeInfoPrefix
+local domain_name = prefixConf.domainname
+
+
+local policy = require("admin/policy")
+local runtime = require('admin/runtime')
+local ab_action = {}
+
+ab_action.policy_check = policy.check
+ab_action.policy_set = policy.set
+ab_action.policy_get = policy.get
+ab_action.policy_del = policy.del
+
+ab_action.runtime_set = runtime.set
+ab_action.runtime_del = runtime.del
+ab_action.runtime_get = runtime.get
+
+local get_uriargs_error = function()
+ local info = ERRORINFO.ACTION_BLANK_ERROR
+ local response = doresp(info, 'user req')
+ dolog(info, desc)
+ ngx.say(response)
+ return
+end
+
+local get_action_error = function()
+ local info = ERRORINFO.ACTION_BLANK_ERROR
+ local response = doresp(info, 'user req')
+ dolog(info, desc)
+ ngx.say(response)
+ return
+end
+
+local do_action_error = function()
+ local info = ERRORINFO.DOACTION_ERROR
+ local desc = action
+ local response = doresp(info, desc)
+ dolog(info, desc)
+ ngx.say(response)
+ return
+end
+
+local red = redisModule:new(redisConf)
+local ok, err = red:connectdb()
+if not ok then
+ local info = ERRORINFO.REDIS_CONNECT_ERROR
+ local response = doresp(info, err)
+ dolog(info, desc)
+ ngx.say(response)
+ return
+end
+
+local args = ngx.req.get_uri_args()
+if args then
+ local action = args.action
+ local do_action = ab_action[action]
+ if do_action then
+ do_action({['db']=red})
+-- local ok, info = do_action(policy, {['db']=red})
+-- if not ok then
+-- do_action_error()
+-- end
+ else
+ doaction_error()
+ end
+else
+ get_uriargs_error()
+end
diff --git a/admin/policy.lua b/admin/policy.lua
new file mode 100644
index 0000000..d7da279
--- /dev/null
+++ b/admin/policy.lua
@@ -0,0 +1,236 @@
+---
+-- @classmod abtesting.adapter.policy
+-- @release 0.0.1
+local modulename = "abtestingAdminPolicy"
+
+local _M = { _VERSION = "0.0.1" }
+local mt = { __index = _M }
+
+local ERRORINFO = require('abtesting.error.errcode').info
+
+local runtimeModule = require('abtesting.adapter.runtime')
+local policyModule = require('abtesting.adapter.policy')
+local redisModule = require('abtesting.utils.redis')
+local systemConf = require('abtesting.utils.init')
+local handler = require('abtesting.error.handler').handler
+local utils = require('abtesting.utils.utils')
+local log = require('abtesting.utils.log')
+local ERRORINFO = require('abtesting.error.errcode').info
+
+local cjson = require('cjson.safe')
+local doresp = utils.doresp
+local dolog = utils.dolog
+local doerror = utils.doerror
+
+local redisConf = systemConf.redisConf
+local divtypes = systemConf.divtypes
+local prefixConf = systemConf.prefixConf
+local policyLib = prefixConf.policyLibPrefix
+local runtimeLib = prefixConf.runtimeInfoPrefix
+local domain_name = prefixConf.domainname
+
+local getPolicyId = function()
+ local policyID = tonumber(ngx.var.arg_policyid)
+
+ if not policyID or policyID < 0 then
+ local info = ERRORINFO.PARAMETER_TYPE_ERROR
+ local desc = "policyID invalid"
+ local response = doresp(info, desc)
+ log:errlog(dolog(info, desc))
+ ngx.say(response)
+ return nil
+ end
+ return policyID
+end
+
+local getPolicy = function()
+
+ local request_body = ngx.var.request_body
+ local postData = cjson.decode(request_body)
+
+ if not request_body then
+ -- ERRORCODE.PARAMETER_NONE
+ local errinfo = ERRORINFO.PARAMETER_NONE
+ local desc = 'request_body or post data'
+ local response = doresp(errinfo, desc)
+ log:errlog(dolog(errinfo, desc))
+ ngx.say(response)
+ return nil
+ end
+
+ if not postData then
+ -- ERRORCODE.PARAMETER_ERROR
+ local errinfo = ERRORINFO.PARAMETER_ERROR
+ local desc = 'postData is not a json string'
+ local response = doresp(errinfo, desc)
+ log:errlog(dolog(errinfo, desc))
+ ngx.say(response)
+ return nil
+ end
+
+ local divtype = postData.divtype
+ local divdata = postData.divdata
+
+ if not divtype or not divdata then
+ -- ERRORCODE.PARAMETER_NONE
+ local errinfo = ERRORINFO.PARAMETER_NONE
+ local desc = "policy divtype or policy divdata"
+ local response = doresp(errinfo, desc)
+ log:errlog(dolog(errinfo, desc))
+ ngx.say(response)
+ return nil
+ end
+
+ if not divtypes[divtype] then
+ -- ERRORCODE.PARAMETER_TYPE_ERROR
+ local errinfo = ERRORINFO.PARAMETER_TYPE_ERROR
+ local desc = "unsupported divtype"
+ local response = doresp(errinfo, desc)
+ log:errlog(dolog(errinfo, desc))
+ ngx.say(response)
+ return nil
+ end
+
+ return postData
+
+end
+
+_M.check = function(option)
+ local db = option.db
+
+ local policy = getPolicy()
+ if not policy then
+ return false
+ end
+
+ local pfunc = function()
+ local policyMod = policyModule:new(db.redis, policyLib)
+ return policyMod:check(policy)
+ end
+
+ local status, info = xpcall(pfunc, handler)
+ if not status then
+ local response = doerror(info)
+ ngx.say(response)
+ return false
+ end
+
+ local chkout = info
+ local valid = chkout[1]
+ local err = chkout[2]
+ local desc = chkout[3]
+
+ local response
+ if not valid then
+ log:errlog(dolog(err, desc))
+ response = doresp(err, desc)
+ else
+ response = doresp(ERRORINFO.SUCCESS)
+ end
+ ngx.say(response)
+ return true
+
+end
+
+_M.set = function(option)
+ local db = option.db
+
+ local policy = getPolicy()
+ if not policy then
+ return false
+ end
+
+ local pfunc = function()
+ policyMod = policyModule:new(db.redis, policyLib)
+ return policyMod:check(policy)
+ end
+
+ local status, info = xpcall(pfunc, handler)
+ if not status then
+ local response = doerror(info)
+ ngx.say(response)
+ return false
+ end
+
+ local chkout = info
+ local valid = chkout[1]
+ local err = chkout[2]
+ local desc = chkout[3]
+
+ if not valid then
+ log:errlog(dolog(err, desc))
+ local response = doresp(err, desc)
+ ngx.say(response)
+ return false
+ end
+
+ local pfunc = function() return policyMod:set(policy) end
+ local status, info = xpcall(pfunc, handler)
+ if not status then
+ local response = doerror(info)
+ ngx.say(response)
+ return false
+ end
+ local data
+ if info then
+ data = ' the id of new policy is '..info
+ end
+
+ local response = doresp(ERRORINFO.SUCCESS, data)
+ ngx.say(response)
+ return true
+
+end
+
+_M.del = function(option)
+ local db = option.db
+
+ local policyId = getPolicyId()
+ if not policyId then
+ return false
+ end
+
+ local pfunc = function()
+ local policyMod = policyModule:new(db.redis, policyLib)
+ return policyMod:del(policyId)
+ end
+
+ local status, info = xpcall(pfunc, handler)
+ if not status then
+ local response = doerror(info)
+ ngx.say(response)
+ return false
+ end
+ local response = doresp(ERRORINFO.SUCCESS)
+ ngx.say(response)
+ return true
+end
+
+_M.get = function(option)
+ local db = option.db
+
+ local policyId = getPolicyId()
+ if not policyId then
+ return false
+ end
+
+ local pfunc = function()
+ local policyIO = policyModule:new(db.redis, policyLib)
+ return policyIO:get(policyId)
+ end
+
+ local status, info = xpcall(pfunc, handler)
+ if not status then
+ local response = doerror(info)
+ ngx.say(response)
+ return false
+ else
+ local response = doresp(ERRORINFO.SUCCESS, nil, info)
+ log:errlog(dolog(ERRORINFO.SUCCESS, nil))
+ ngx.say(response)
+ return true
+ end
+
+end
+
+return _M
diff --git a/admin/policy/check.lua b/admin/policy/check.lua
deleted file mode 100644
index 176e4f5..0000000
--- a/admin/policy/check.lua
+++ /dev/null
@@ -1,103 +0,0 @@
-local policyModule = require('abtesting.adapter.policy')
-local redisModule = require('abtesting.utils.redis')
-local systemConf = require('abtesting.utils.init')
-local handler = require('abtesting.error.handler').handler
-local utils = require('abtesting.utils.utils')
-local ERRORINFO = require('abtesting.error.errcode').info
-
-local cjson = require('cjson.safe')
-local doresp = utils.doresp
-local dolog = utils.dolog
-
-local redisConf = systemConf.redisConf
-local divtypes = systemConf.divtypes
-local prefixConf = systemConf.prefixConf
-local policyLib = prefixConf.policyLibPrefix
-
-local request_body = ngx.var.request_body
-local postData = cjson.decode(request_body)
-
-if not request_body then
- -- ERRORCODE.PARAMETER_NONE
- local errinfo = ERRORINFO.PARAMETER_NONE
- local desc = 'request_body or post data'
- local response = doresp(errinfo, desc)
- dolog(errinfo, desc)
- ngx.say(response)
- return
-end
-
-if not postData then
- -- ERRORCODE.PARAMETER_ERROR
- local errinfo = ERRORINFO.PARAMETER_ERROR
- local desc = 'postData is not a json string'
- local response = doresp(errinfo, desc)
- dolog(errinfo, desc)
- ngx.say(response)
- return
-end
-
-local divtype = postData.divtype
-local divdata = postData.divdata
-
-if not divtype or not divdata then
- -- ERRORCODE.PARAMETER_NONE
- local errinfo = ERRORINFO.PARAMETER_NONE
- local desc = "policy divtype or policy divdata"
- local response = doresp(errinfo, desc)
- dolog(errinfo, desc)
- ngx.say(response)
- return
-end
-
-if not divtypes[divtype] then
- -- ERRORCODE.PARAMETER_TYPE_ERROR
- local errinfo = ERRORINFO.PARAMETER_TYPE_ERROR
- local desc = "unsupported divtype"
- local response = doresp(errinfo, desc)
- dolog(errinfo, desc)
- ngx.say(response)
- return
-end
-
-local red = redisModule:new(redisConf)
-local ok, err = red:connectdb()
-if not ok then
- local errinfo = ERRORINFO.REDIS_CONNECT_ERROR
- local response = doresp(errinfo, err)
- dolog(errinfo, err)
- ngx.say(response)
- return
-end
-
-local pfunc = function()
- local policyMod = policyModule:new(red.redis, policyLib)
- local policy = postData
- return policyMod:check(policy)
-end
-
-local status, info = xpcall(pfunc, handler)
-if not status then
- local errinfo = info[1]
- local errstack = info[2]
- local err, desc = errinfo[1], errinfo[2]
- local response = doresp(err, desc)
- dolog(err, desc, nil, errstack)
- ngx.say(response)
- return
-end
-
-local chkout = info
-local valid = chkout[1]
-local err = chkout[2]
-local desc = chkout[3]
-
-local response
-if not valid then
- dolog(err, desc)
- response = doresp(err, desc)
-else
- response = doresp(ERRORINFO.SUCCESS)
-end
-ngx.say(response)
-
diff --git a/admin/policy/del.lua b/admin/policy/del.lua
deleted file mode 100644
index 83ca471..0000000
--- a/admin/policy/del.lua
+++ /dev/null
@@ -1,143 +0,0 @@
-local runtimeModule = require('abtesting.adapter.runtime')
-local policyModule = require('abtesting.adapter.policy')
-local redisModule = require('abtesting.utils.redis')
-local systemConf = require('abtesting.utils.init')
-local handler = require('abtesting.error.handler').handler
-local utils = require('abtesting.utils.utils')
-local ERRORINFO = require('abtesting.error.errcode').info
-
-local cjson = require('cjson.safe')
-local doresp = utils.doresp
-local dolog = utils.dolog
-
-local redisConf = systemConf.redisConf
-local divtypes = systemConf.divtypes
-local prefixConf = systemConf.prefixConf
-local policyLib = prefixConf.policyLibPrefix
-local runtimeLib = prefixConf.runtimeInfoPrefix
-local domain_name = prefixConf.domainname
-
-local policyID = ngx.var.arg_policyid
-
-if policyID then
- policyID = tonumber(ngx.var.arg_policyid)
- if not policyID or policyID < 0 then
- local info = ERRORINFO.PARAMETER_TYPE_ERROR
- local desc = "policyID should be a positive Integer"
- local response = doresp(info, desc)
- dolog(info, desc)
- ngx.say(response)
- return
- end
-end
-
-if not policyID then
- local request_body = ngx.var.request_body
- local postData = cjson.decode(request_body)
-
- if not request_body then
- -- ERRORCODE.PARAMETER_NONE
- local info = ERRORINFO.PARAMETER_NONE
- local desc = 'request_body or post data to get policyID'
- local response = doresp(info, desc)
- dolog(info, desc)
- ngx.say(response)
- return
- end
-
- if not postData then
- -- ERRORCODE.PARAMETER_ERROR
- local info = ERRORINFO.PARAMETER_ERROR
- local desc = 'postData is not a json string'
- local response = doresp(info, desc)
- dolog(info, desc)
- ngx.say(response)
- return
- end
-
- policyID = postData.policyid
-
- if not policyID then
- local info = ERRORINFO.PARAMETER_ERROR
- local desc = "policyID is needed"
- local response = doresp(info, desc)
- dolog(info, desc)
- ngx.say(response)
- return
- end
-
- policyID = tonumber(postData.policyid)
-
- if not policyID or policyID < 0 then
- local info = ERRORINFO.PARAMETER_TYPE_ERROR
- local desc = "policyID should be a positive Integer"
- local response = doresp(info, desc)
- dolog(info, desc)
- ngx.say(response)
- return
- end
-end
-
-local red = redisModule:new(redisConf)
-local ok, err = red:connectdb()
-if not ok then
- local info = ERRORINFO.REDIS_CONNECT_ERROR
- local response = doresp(info, err)
- dolog(info, desc)
- ngx.say(response)
- return
-end
-
-
-local pfunc = function()
- local runtimeMod = runtimeModule:new(red.redis, runtimeLib)
- return runtimeMod:get(domain_name)
-end
-
-local status, info = xpcall(pfunc, handler)
-if not status then
- local errinfo = info[1]
- local errstack = info[2]
- local err, desc = errinfo[1], errinfo[2]
- local response = doresp(err, desc)
- dolog(err, desc, nil, errstack)
- ngx.say(response)
- return
-end
-
-local divModname = info[1]
-local divPolicy = info[2]
-local userInfoModname = info[3]
-
-if divPolicy and divPolicy ~= ngx.null then
- local s, e = string.find(divPolicy, policyLib)
- if s and e then
- local sub = string.sub(divPolicy, e+1)
- local _, _, num = string.find(sub, "(%d+)")
- num = tonumber(num)
- if num and num == policyID then
- local response = doresp(ERRORINFO.POLICY_BUSY_ERROR, policyID)
- ngx.say(response)
- return
- end
- end
-end
-
-local pfunc = function()
- local policyMod = policyModule:new(red.redis, policyLib)
- return policyMod:del(policyID)
-end
-
-local status, info = xpcall(pfunc, handler)
-if not status then
- local errinfo = info[1]
- local errstack = info[2]
- local err, desc = errinfo[1], errinfo[2]
- local response = doresp(err, desc)
- dolog(err, desc, nil, errstack)
- ngx.say(response)
- return
-end
-
-local response = doresp(ERRORINFO.SUCCESS)
-ngx.say(response)
diff --git a/admin/policy/get.lua b/admin/policy/get.lua
deleted file mode 100644
index d75036c..0000000
--- a/admin/policy/get.lua
+++ /dev/null
@@ -1,107 +0,0 @@
-local policyModule = require('abtesting.adapter.policy')
-local redisModule = require('abtesting.utils.redis')
-local systemConf = require('abtesting.utils.init')
-local handler = require('abtesting.error.handler').handler
-local utils = require('abtesting.utils.utils')
-local ERRORINFO = require('abtesting.error.errcode').info
-local cjson = require('cjson.safe')
-
-local redisConf = systemConf.redisConf
-local divtypes = systemConf.divtypes
-local prefixConf = systemConf.prefixConf
-local policyLib = prefixConf.policyLibPrefix
-
-local doresp = utils.doresp
-local dolog = utils.dolog
-
-local policyID = ngx.var.arg_policyid
-
-if policyID then
- policyID = tonumber(ngx.var.arg_policyid)
- if not policyID or policyID < 0 then
- local info = ERRORINFO.PARAMETER_TYPE_ERROR
- local desc = "policyID should be a positive Integer"
- local response = doresp(info, desc)
- dolog(info, desc)
- ngx.say(response)
- return
- end
-end
-
-if not policyID then
- local request_body = ngx.var.request_body
- local postData = cjson.decode(request_body)
-
- if not request_body then
- -- ERRORCODE.PARAMETER_NONE
- local info = ERRORINFO.PARAMETER_NONE
- local desc = 'request_body or post data to get policyID'
- local response = doresp(info, desc)
- dolog(info, desc)
- ngx.say(response)
- return
- end
-
- if not postData then
- -- ERRORCODE.PARAMETER_ERROR
- local info = ERRORINFO.PARAMETER_ERROR
- local desc = 'postData is not a json string'
- local response = doresp(info, desc)
- dolog(info, desc)
- ngx.say(response)
- return
- end
-
- policyID = postData.policyid
-
- if not policyID then
- local info = ERRORINFO.PARAMETER_ERROR
- local desc = "policyID is needed"
- local response = doresp(info, desc)
- dolog(info, desc)
- ngx.say(response)
- return
- end
-
- policyID = tonumber(postData.policyid)
-
- if not policyID or policyID < 0 then
- local info = ERRORINFO.PARAMETER_TYPE_ERROR
- local desc = "policyID should be a positive Integer"
- local response = doresp(info, desc)
- dolog(info, desc)
- ngx.say(response)
- return
- end
-end
-
-local red = redisModule:new(redisConf)
-local ok, err = red:connectdb()
-if not ok then
- local info = ERRORINFO.REDIS_CONNECT_ERROR
- local response = doresp(info, err)
- dolog(info, desc)
- ngx.say(response)
- return
-end
-
-local pfunc = function()
- local policyIO = policyModule:new(red.redis, policyLib)
- return policyIO:get(policyID)
-end
-
-local status, info = xpcall(pfunc, handler)
-if not status then
- local errinfo = info[1]
- local errstack = info[2]
- local err, desc = errinfo[1], errinfo[2]
- local response = doresp(err, desc)
- dolog(err, desc, nil, errstack)
- ngx.say(response)
- return
-else
- local response = doresp(ERRORINFO.SUCCESS, nil, info)
- dolog(ERRORINFO.SUCCESS, nil)
- ngx.say(response)
-end
-
diff --git a/admin/policy/set.lua b/admin/policy/set.lua
deleted file mode 100644
index a606ccd..0000000
--- a/admin/policy/set.lua
+++ /dev/null
@@ -1,124 +0,0 @@
-local policyModule = require('abtesting.adapter.policy')
-local redisModule = require('abtesting.utils.redis')
-local systemConf = require('abtesting.utils.init')
-local handler = require('abtesting.error.handler').handler
-local utils = require('abtesting.utils.utils')
-local ERRORINFO = require('abtesting.error.errcode').info
-
-local cjson = require('cjson.safe')
-local doresp = utils.doresp
-local dolog = utils.dolog
-
-local redisConf = systemConf.redisConf
-local divtypes = systemConf.divtypes
-local prefixConf = systemConf.prefixConf
-local policyLib = prefixConf.policyLibPrefix
-
-local request_body = ngx.var.request_body
-local postData = cjson.decode(request_body)
-
-if not request_body then
- -- ERRORCODE.PARAMETER_NONE
- local errinfo = ERRORINFO.PARAMETER_NONE
- local desc = 'request_body or post data'
- local response = doresp(errinfo, desc)
- dolog(errinfo, desc)
- ngx.say(response)
- return
-end
-
-if not postData then
- -- ERRORCODE.PARAMETER_ERROR
- local errinfo = ERRORINFO.PARAMETER_ERROR
- local desc = 'postData is not a json string'
- local response = doresp(errinfo, desc)
- dolog(errinfo, desc)
- ngx.say(response)
- return
-end
-
-local divtype = postData.divtype
-local divdata = postData.divdata
-
-if not divtype or not divdata then
- -- ERRORCODE.PARAMETER_NONE
- local errinfo = ERRORINFO.PARAMETER_NONE
- local desc = "policy divtype or policy divdata"
- local response = doresp(errinfo, desc)
- dolog(errinfo, desc)
- ngx.say(response)
- return
-end
-
-if not divtypes[divtype] then
- -- ERRORCODE.PARAMETER_TYPE_ERROR
- local errinfo = ERRORINFO.PARAMETER_TYPE_ERROR
- local desc = "unsupported divtype"
- local response = doresp(errinfo, desc)
- dolog(errinfo, desc)
- ngx.say(response)
- return
-end
-
-local red = redisModule:new(redisConf)
-local ok, err = red:connectdb()
-if not ok then
- -- ERRORCODE.REDIS_CONNECT_ERROR
- -- connect to redis error
- local errinfo = ERRORINFO.REDIS_CONNECT_ERROR
- local response = doresp(errinfo, err)
- dolog(errinfo, err)
- ngx.say(response)
- return
-end
-
-local policyMod
-local policy = postData
-
-local pfunc = function()
- policyMod = policyModule:new(red.redis, policyLib)
- return policyMod:check(policy)
-end
-
-local status, info = xpcall(pfunc, handler)
-if not status then
- local errinfo = info[1]
- local errstack = info[2]
- local err, desc = errinfo[1], errinfo[2]
- local response = doresp(err, desc)
- dolog(err, desc, nil, errstack)
- ngx.say(response)
- return
-end
-
-local chkout = info
-local valid = chkout[1]
-local err = chkout[2]
-local desc = chkout[3]
-
-if not valid then
- dolog(err, desc)
- local response = doresp(err, desc)
- ngx.say(response)
- return
-end
-
-local pfunc = function() return policyMod:set(policy) end
-local status, info = xpcall(pfunc, handler)
-if not status then
- local errinfo = info[1]
- local errstack = info[2]
- local err, desc = errinfo[1], errinfo[2]
- local response = doresp(err, desc)
- dolog(err, desc, nil, errstack)
- ngx.say(response)
- return
-end
-
-local data
-if info then
- data = ' the id of new policy is '..info
-end
-
-local response = doresp(ERRORINFO.SUCCESS, data)
-ngx.say(response)
diff --git a/admin/policygroup.lua b/admin/policygroup.lua
new file mode 100644
index 0000000..5fbe109
--- /dev/null
+++ b/admin/policygroup.lua
@@ -0,0 +1,269 @@
+---
+-- @classmod abtesting.adapter.policy
+-- @release 0.0.1
+local modulename = "abtestingAdminPolicyGroup"
+
+local _M = { _VERSION = "0.0.1" }
+local mt = { __index = _M }
+
+local ERRORINFO = require('abtesting.error.errcode').info
+
+local runtimeModule = require('abtesting.adapter.runtime')
+local policyModule = require('abtesting.adapter.policy')
+local redisModule = require('abtesting.utils.redis')
+local systemConf = require('abtesting.utils.init')
+local handler = require('abtesting.error.handler').handler
+local utils = require('abtesting.utils.utils')
+local log = require('abtesting.utils.log')
+local ERRORINFO = require('abtesting.error.errcode').info
+
+local cjson = require('cjson.safe')
+local doresp = utils.doresp
+local dolog = utils.dolog
+local doerror = utils.doerror
+
+local redisConf = systemConf.redisConf
+local divtypes = systemConf.divtypes
+local prefixConf = systemConf.prefixConf
+local policyLib = prefixConf.policyLibPrefix
+local runtimeLib = prefixConf.runtimeInfoPrefix
+local domain_name = prefixConf.domainname
+
+local policyGroupModule = require('abtesting.adapter.policygroup')
+local policyGroupLib = prefixConf.policyGroupPrefix
+
+local getPolicyGroupId = function()
+ local policyGroupId = tonumber(ngx.var.arg_policygroupid)
+ if not policyGroupId or policyGroupId < 0 then
+ local info = ERRORINFO.PARAMETER_TYPE_ERROR
+ local desc = "policyGroupId invalid"
+ local response = doresp(info, desc)
+ log:errlog(dolog(info, desc))
+ ngx.say(response)
+ return nil
+ end
+ return policyGroupId
+end
+
+local getPolicyGroup = function()
+
+ local request_body = ngx.var.request_body
+ local postData = cjson.decode(request_body)
+
+ if not request_body then
+ -- ERRORCODE.PARAMETER_NONE
+ local errinfo = ERRORINFO.PARAMETER_NONE
+ local desc = 'request_body or post data'
+ local response = doresp(errinfo, desc)
+ log:errlog(dolog(errinfo, desc))
+ ngx.say(response)
+ return nil
+ end
+
+ if not postData then
+ -- ERRORCODE.PARAMETER_ERROR
+ local errinfo = ERRORINFO.PARAMETER_ERROR
+ local desc = 'postData is not a json string'
+ local response = doresp(errinfo, desc)
+ log:errlog(dolog(errinfo, desc))
+ ngx.say(response)
+ return nil
+ end
+
+ local policy_cnt = 0
+ local policyGroup = {}
+ for k, v in pairs(postData) do
+ policy_cnt = policy_cnt + 1
+
+ local idx = tonumber(k)
+ if not idx or type(v) ~= 'table' then
+ local errinfo = ERRORINFO.PARAMETER_ERROR
+ local desc = 'policyGroup error'
+ local response = doresp(errinfo, desc)
+ log:errlog(dolog(errinfo, desc))
+ ngx.say(response)
+ return nil
+ end
+
+ local policy = v
+ local divtype = policy.divtype
+ local divdata = policy.divdata
+
+ if not divtype or not divdata then
+ -- ERRORCODE.PARAMETER_NONE
+ local errinfo = ERRORINFO.PARAMETER_NONE
+ local desc = "policy divtype or policy divdata"
+ local response = doresp(errinfo, desc)
+ log:errlog(dolog(errinfo, desc))
+ ngx.say(response)
+ return nil
+ end
+
+ if not divtypes[divtype] then
+ -- ERRORCODE.PARAMETER_TYPE_ERROR
+ local errinfo = ERRORINFO.PARAMETER_TYPE_ERROR
+ local desc = "unsupported divtype"
+ local response = doresp(errinfo, desc)
+ log:errlog(dolog(errinfo, desc))
+ ngx.say(response)
+ return nil
+ end
+
+ if policyGroup[idx] then
+ --不能混淆,优先级不能重复
+ local errinfo = ERRORINFO.PARAMETER_TYPE_ERROR
+ local desc = "policy in policy group should not overlap"
+ local response = doresp(errinfo, desc)
+ log:errlog(dolog(errinfo, desc))
+ ngx.say(response)
+ return nil
+ end
+
+ policyGroup[idx] = policy
+ end
+
+ if policy_cnt ~= #policyGroup then
+ local errinfo = ERRORINFO.PARAMETER_TYPE_ERROR
+ local desc = "index of policy in policy_group should be one by one"
+ local response = doresp(errinfo, desc)
+ log:errlog(dolog(errinfo, desc))
+ ngx.say(response)
+ return nil
+ end
+
+ return policyGroup
+end
+
+_M.checkPolicy = function(option)
+ local db = option.db
+
+ local policyGroup = getPolicyGroup()
+ if not policyGroup then
+ return false
+ end
+
+ local steps = #policyGroup
+ if steps < 1 then
+ local errinfo = ERRORINFO.PARAMETER_NONE
+ local desc = "blank policy group"
+ local response = doresp(errinfo, desc)
+ log:errlog(dolog(errinfo, desc))
+ ngx.say(response)
+ return false
+ end
+
+ local pfunc = function()
+ local policyGroupMod = policyGroupModule:new(db.redis,
+ policyGroupLib, policyLib)
+ return policyGroupMod:check(policyGroup)
+ end
+ local status, info = xpcall(pfunc, handler)
+ if not status then
+ local response = doerror(info)
+ ngx.say(response)
+ return false
+ end
+
+ local chkout = info
+ local valid = chkout[1]
+ local err = chkout[2]
+ local desc = chkout[3]
+
+ if not valid then
+ local response = doresp(err, desc)
+ ngx.say(response)
+ log:errlog(dolog(err, desc))
+ return false
+ end
+
+ return true
+end
+
+_M.check = function(option)
+ local status = _M.checkPolicy(option)
+ if not status then return end
+ local response = doresp(ERRORINFO.SUCCESS)
+ ngx.say(response)
+ return true
+end
+
+_M.set = function(option)
+
+ local status = _M.checkPolicy(option)
+ if not status then return end
+
+ local db = option.db
+
+ local policyGroup = getPolicyGroup()
+ if not policyGroup then
+ return false
+ end
+
+ local pfunc = function()
+ local policyGroupMod = policyGroupModule:new(db.redis,
+ policyGroupLib, policyLib)
+ return policyGroupMod:set(policyGroup)
+ end
+ local status, info = xpcall(pfunc, handler)
+ if not status then
+ local response = doerror(info)
+ ngx.say(response)
+ return false
+ end
+
+ local data = info
+ local response = doresp(ERRORINFO.SUCCESS, _, data)
+ ngx.say(response)
+ return true
+end
+
+_M.get = function(option)
+ local db = option.db
+
+ local policyGroupId = getPolicyGroupId()
+ if not policyGroupId then
+ return false
+ end
+
+ local pfunc = function()
+ local policyGroupMod = policyGroupModule:new(db.redis,
+ policyGroupLib, policyLib)
+ return policyGroupMod:get(policyGroupId)
+ end
+ local status, info = xpcall(pfunc, handler)
+ if not status then
+ local response = doerror(info)
+ ngx.say(response)
+ return false
+ end
+ local data = info
+ local response = doresp(ERRORINFO.SUCCESS, _, data)
+ ngx.say(response)
+ return true
+end
+
+_M.del = function(option)
+ local db = option.db
+
+ local policyGroupId = getPolicyGroupId()
+ if not policyGroupId then
+ return false
+ end
+
+ local pfunc = function()
+ local policyGroupMod = policyGroupModule:new(db.redis,
+ policyGroupLib, policyLib)
+ return policyGroupMod:del(policyGroupId)
+ end
+ local status, info = xpcall(pfunc, handler)
+ if not status then
+ local response = doerror(info)
+ ngx.say(response)
+ return false
+ end
+ local response = doresp(ERRORINFO.SUCCESS)
+ ngx.say(response)
+ return true
+end
+
+return _M
diff --git a/admin/runtime.lua b/admin/runtime.lua
new file mode 100644
index 0000000..28d9547
--- /dev/null
+++ b/admin/runtime.lua
@@ -0,0 +1,239 @@
+---
+-- @classmod abtesting.adapter.policy
+-- @release 0.0.1
+local modulename = "abtestingAdminRuntime"
+
+local _M = { _VERSION = "0.0.1" }
+local mt = { __index = _M }
+
+local ERRORINFO = require('abtesting.error.errcode').info
+
+local runtimeModule = require('abtesting.adapter.runtime')
+local policyModule = require('abtesting.adapter.policy')
+local redisModule = require('abtesting.utils.redis')
+local systemConf = require('abtesting.utils.init')
+local handler = require('abtesting.error.handler').handler
+local utils = require('abtesting.utils.utils')
+local log = require('abtesting.utils.log')
+local ERRORINFO = require('abtesting.error.errcode').info
+local cjson = require('cjson.safe')
+
+local redisConf = systemConf.redisConf
+local prefixConf = systemConf.prefixConf
+local runtimeLib = prefixConf.runtimeInfoPrefix
+local policyLib = prefixConf.policyLibPrefix
+local domain_name = prefixConf.domainname
+local divtypes = systemConf.divtypes
+local fields = systemConf.fields
+
+local runtimeGroupModule = require('abtesting.adapter.runtimegroup')
+local policyGroupModule = require('abtesting.adapter.policygroup')
+local policyGroupLib = prefixConf.policyGroupPrefix
+
+
+local doresp = utils.doresp
+local dolog = utils.dolog
+local doerror = utils.doerror
+
+local getPolicyId = function()
+ local policyID = tonumber(ngx.var.arg_policyid)
+ return policyID
+end
+
+local getPolicyGroupId = function()
+ local policyGroupId = tonumber(ngx.var.arg_policygroupid)
+ return policyGroupId
+end
+
+local getHostName = function()
+ local hostname = ngx.var.arg_hostname
+ return hostname
+end
+
+local getDivSteps = function()
+ local divsteps = tonumber(ngx.var.arg_divsteps)
+ return divsteps
+end
+
+_M.get = function(option)
+ local db = option.db
+ local database = db.redis
+
+ local hostname = getHostName()
+ if not hostname or string.len(hostname) < 1 or hostname == ngx.null then
+ local info = ERRORINFO.PARAMETER_TYPE_ERROR
+ local desc = 'arg hostname invalid: '
+ local response = doresp(info, desc)
+ log:errlog(dolog(info, desc))
+ ngx.say(response)
+ return nil
+ end
+
+ local pfunc = function()
+ local runtimeGroupMod = runtimeGroupModule:new(database, runtimeLib)
+ return runtimeGroupMod:get(hostname)
+ end
+ local status, info = xpcall(pfunc, handler)
+ if not status then
+ local response = doerror(info)
+ ngx.say(response)
+ return false
+ end
+
+ local response = doresp(ERRORINFO.SUCCESS, nil, info)
+ ngx.say(response)
+ return true
+end
+
+_M.del = function(option)
+ local db = option.db
+ local database = db.redis
+
+ local hostname = getHostName()
+ if not hostname or string.len(hostname) < 1 or hostname == ngx.null then
+ local info = ERRORINFO.PARAMETER_TYPE_ERROR
+ local desc = 'arg hostname invalid: '
+ local response = doresp(info, desc)
+ log:errlog(dolog(info, desc))
+ ngx.say(response)
+ return nil
+ end
+
+ local pfunc = function()
+ local runtimeGroupMod = runtimeGroupModule:new(database, runtimeLib)
+ return runtimeGroupMod:del(hostname)
+ end
+ local status, info = xpcall(pfunc, handler)
+ if not status then
+ local response = doerror(info)
+ ngx.say(response)
+ return false
+ end
+
+ local response = doresp(ERRORINFO.SUCCESS)
+ ngx.say(response)
+ return true
+end
+
+_M.set = function(option)
+ local policyId = getPolicyId()
+ local policyGroupId = getPolicyGroupId()
+
+ if policyId and policyId >= 0 then
+ _M.runtimeset(option, policyId)
+ elseif policyGroupId and policyGroupId >= 0 then
+ _M.groupset(option, policyGroupId)
+ else
+ local info = ERRORINFO.PARAMETER_TYPE_ERROR
+ local desc = "policyId or policyGroupid invalid"
+ local response = doresp(info, desc)
+ log:errlog(dolog(info, desc))
+ ngx.say(response)
+ return nil
+ end
+end
+
+_M.groupset = function(option, policyGroupId)
+ local db = option.db
+ local database = db.redis
+
+ local hostname = getHostName()
+ local divsteps = getDivSteps()
+
+ if not hostname or string.len(hostname) < 1 or hostname == ngx.null then
+ local info = ERRORINFO.PARAMETER_TYPE_ERROR
+ local desc = 'arg hostname invalid: '
+ local response = doresp(info, desc)
+ log:errlog(dolog(info, desc))
+ ngx.say(response)
+ return nil
+ end
+
+ local pfunc = function()
+ local runtimeGroupMod = runtimeGroupModule:new(database, runtimeLib)
+ runtimeGroupMod:del(hostname)
+ return runtimeGroupMod:set(hostname, policyGroupId, divsteps)
+ end
+ local status, info = xpcall(pfunc, handler)
+ if not status then
+ local response = doerror(info)
+ ngx.say(response)
+ return false
+ end
+
+ local response = doresp(ERRORINFO.SUCCESS)
+ ngx.say(response)
+ return true
+
+end
+
+_M.runtimeset = function(option, policyId)
+ local db = option.db
+ local database = db.redis
+
+ local hostname = getHostName()
+ local divsteps = 1
+
+ if not hostname or string.len(hostname) < 1 or hostname == ngx.null then
+ local info = ERRORINFO.PARAMETER_TYPE_ERROR
+ local desc = 'arg hostname invalid: '
+ local response = doresp(info, desc)
+ log:errlog(dolog(info, desc))
+ ngx.say(response)
+ return nil
+ end
+
+ local pfunc = function()
+ local runtimeGroupMod = runtimeGroupModule:new(database, runtimeLib)
+ return runtimeGroupMod:del(hostname)
+ end
+ local status, info = xpcall(pfunc, handler)
+ if not status then
+ local response = doerror(info)
+ ngx.say(response)
+ return false
+ end
+
+ local pfunc = function()
+ local policyMod = policyModule:new(database, policyLib)
+ local policy = policyMod:get(policyId)
+
+ local divtype = policy.divtype
+ local divdata = policy.divdata
+
+ if divtype == ngx.null or divdata == ngx.null then
+ error{ERRORINFO.POLICY_BLANK_ERROR, 'policy NO '..policyId}
+ end
+
+ if not divtypes[divtype] then
+
+ end
+
+ local prefix = hostname .. ':first'
+ local divModulename = table.concat({'abtesting', 'diversion', divtype}, '.')
+ local divDataKey = table.concat({policyLib, policyId, fields.divdata}, ':')
+ local userInfoModulename = table.concat({'abtesting', 'userinfo', divtypes[divtype]}, '.')
+ local runtimeMod = runtimeModule:new(database, runtimeLib)
+ runtimeMod:set(prefix, divModulename, divDataKey, userInfoModulename)
+
+ local divSteps = runtimeLib .. ':' .. hostname .. ':' .. fields.divsteps
+ local ok, err = database:set(divSteps, 1)
+ if not ok then error{ERRORINFO.REDIS_ERROR, err} end
+ end
+
+ local status, info = xpcall(pfunc, handler)
+ if not status then
+ local response = doerror(info)
+ ngx.say(response)
+ return false
+ end
+
+
+ local response = doresp(ERRORINFO.SUCCESS)
+ ngx.say(response)
+ return true
+end
+
+
+
+return _M
diff --git a/admin/runtime/del.lua b/admin/runtime/del.lua
deleted file mode 100644
index 6d989e0..0000000
--- a/admin/runtime/del.lua
+++ /dev/null
@@ -1,85 +0,0 @@
-local runtimeModule = require('abtesting.adapter.runtime')
-local redisModule = require('abtesting.utils.redis')
-local systemConf = require('abtesting.utils.init')
-local handler = require('abtesting.error.handler').handler
-local utils = require('abtesting.utils.utils')
-local ERRORINFO = require('abtesting.error.errcode').info
-local cjson = require('cjson.safe')
-
-local redisConf = systemConf.redisConf
-local prefixConf = systemConf.prefixConf
-local runtimeLib = prefixConf.runtimeInfoPrefix
-local policyLib = prefixConf.policyLibPrefix
-local domain_name = prefixConf.domainname
-local divtypes = systemConf.divtypes
-
-local doresp = utils.doresp
-local dolog = utils.dolog
-
-local domainName = domain_name or ngx.var.arg_domainname
-if not domainName then
- local request_body = ngx.var.request_body
- local postData = cjson.decode(request_body)
-
- if not request_body then
- -- ERRORCODE.PARAMETER_NONE
- local info = ERRORINFO.PARAMETER_NONE
- local desc = 'request_body or post data'
- local response = doresp(info, desc)
- dolog(info, desc)
- ngx.say(response)
- return
- end
-
- if not postData then
- -- ERRORCODE.PARAMETER_ERROR
- local info = ERRORINFO.PARAMETER_ERROR
- local desc = 'postData is not a json string'
- local response = doresp(info, desc)
- dolog(info, desc)
- ngx.say(response)
- return
- end
-
- if not domainName then
- domainName = postData.domainname
- if not domainName then
- local info = ERRORINFO.PARAMETER_NONE
- local desc = "domainName"
- local response = doresp(info, desc)
- dolog(info, desc)
- ngx.say(response)
- return
- end
- end
-end
-
-
-local red = redisModule:new(redisConf)
-local ok, err = red:connectdb()
-if not ok then
- local errinfo = ERRORINFO.REDIS_CONNECT_ERROR
- local response = doresp(errinfo, err)
- dolog(errinfo, err)
- ngx.say(response)
- return
-end
-
-local pfunc = function()
- local runtimeMod = runtimeModule:new(red.redis, runtimeLib)
- runtimeMod:del(domainName)
-end
-
-local status, info = xpcall(pfunc, handler)
-if not status then
- local errinfo = info[1]
- local errstack = info[2]
- local err, desc = errinfo[1], errinfo[2]
- local response = doresp(err, desc)
- dolog(err, desc, nil, errstack)
- ngx.say(response)
- return
-end
-
-local response = doresp(ERRORINFO.SUCCESS)
-ngx.say(response)
diff --git a/admin/runtime/get.lua b/admin/runtime/get.lua
deleted file mode 100644
index b2e7bc4..0000000
--- a/admin/runtime/get.lua
+++ /dev/null
@@ -1,100 +0,0 @@
-local runtimeModule = require('abtesting.adapter.runtime')
-local redisModule = require('abtesting.utils.redis')
-local systemConf = require('abtesting.utils.init')
-local handler = require('abtesting.error.handler').handler
-local utils = require('abtesting.utils.utils')
-local ERRORINFO = require('abtesting.error.errcode').info
-local cjson = require('cjson.safe')
-
-local redisConf = systemConf.redisConf
-local prefixConf = systemConf.prefixConf
-local runtimeLib = prefixConf.runtimeInfoPrefix
-local policyLib = prefixConf.policyLibPrefix
-local domain_name = prefixConf.domainname
-local divtypes = systemConf.divtypes
-
-local fields = {}
-fields.divModulename = 'divModulename'
-fields.divDataKey = 'divDataKey'
-fields.userInfoModulename = 'userInfoModulename'
-
-local doresp = utils.doresp
-local dolog = utils.dolog
-
-local domainName = domain_name or ngx.var.arg_domainname
-
-if not domainName then
- local request_body = ngx.var.request_body
- local postData = cjson.decode(request_body)
-
- if not request_body then
- -- ERRORCODE.PARAMETER_NONE
- local info = ERRORINFO.PARAMETER_NONE
- local desc = 'request_body or post data'
- local response = doresp(info, desc)
- dolog(info, desc)
- ngx.say(response)
- return
- end
-
- if not postData then
- -- ERRORCODE.PARAMETER_ERROR
- local info = ERRORINFO.PARAMETER_ERROR
- local desc = 'postData is not a json string'
- local response = doresp(info, desc)
- dolog(info, desc)
- ngx.say(response)
- return
- end
-
- if not domainName then
- domainName = postData.domainname
- if not domainName then
- local info = ERRORINFO.PARAMETER_NONE
- local desc = "domainName"
- local response = doresp(info, desc)
- dolog(info, desc)
- ngx.say(response)
- return
- end
- end
-end
-
-
-local red = redisModule:new(redisConf)
-local ok, err = red:connectdb()
-if not ok then
- local errinfo = ERRORINFO.REDIS_CONNECT_ERROR
- local response = doresp(errinfo, err)
- dolog(errinfo, err)
- ngx.say(response)
- return
-end
-
-local pfunc = function()
- local runtimeMod = runtimeModule:new(red.redis, runtimeLib)
- return runtimeMod:get(domainName)
-end
-
-local status, info = xpcall(pfunc, handler)
-if not status then
- local errinfo = info[1]
- local errstack = info[2]
- local err, desc = errinfo[1], errinfo[2]
- local response = doresp(err, desc)
- dolog(err, desc, nil, errstack)
- ngx.say(response)
- return
-else
- divModulename = fields.divModulename
- divDataKey = fields.divDataKey
- userInfoModulename = fields.userInfoModulename
- local runtimeInfo = {}
- runtimeInfo[divModulename] = info[1]
- runtimeInfo[divDataKey] = info[2]
- runtimeInfo[userInfoModulename] = info[3]
-
- local response = doresp(ERRORINFO.SUCCESS, nil, runtimeInfo)
- ngx.say(response)
-end
-
diff --git a/admin/runtime/set.lua b/admin/runtime/set.lua
deleted file mode 100644
index 0b80587..0000000
--- a/admin/runtime/set.lua
+++ /dev/null
@@ -1,162 +0,0 @@
-local runtimeModule = require('abtesting.adapter.runtime')
-local policyModule = require('abtesting.adapter.policy')
-local redisModule = require('abtesting.utils.redis')
-local systemConf = require('abtesting.utils.init')
-local handler = require('abtesting.error.handler').handler
-local utils = require('abtesting.utils.utils')
-local ERRORINFO = require('abtesting.error.errcode').info
-local cjson = require('cjson.safe')
-
-local redisConf = systemConf.redisConf
-local prefixConf = systemConf.prefixConf
-local runtimeLib = prefixConf.runtimeInfoPrefix
-local policyLib = prefixConf.policyLibPrefix
-local domain_name = prefixConf.domainname
-local divtypes = systemConf.divtypes
-
-local separator = ':'
-local fields = {}
-fields.divtype = 'divtype'
-fields.divdata = 'divdata'
-fields.idCount = 'idCount'
-
-local doresp = utils.doresp
-local dolog = utils.dolog
-
-local domainName = domain_name
-if not domainName or domainName == ngx.null
- or string.len(domainName) < 1 then
- local info = ERRORINFO.PARAMETER_NONE
- local desc = "domainName is blank and please set it in nginx.conf"
- local response = doresp(info, desc)
- dolog(info, desc)
- ngx.say(response)
- return
-end
-
-local policyID = ngx.var.arg_policyid
-
-if policyID then
- policyID = tonumber(ngx.var.arg_policyid)
- if not policyID or policyID < 0 then
- local info = ERRORINFO.PARAMETER_TYPE_ERROR
- local desc = "policyID should be a positive Integer"
- local response = doresp(info, desc)
- dolog(info, desc)
- ngx.say(response)
- return
- end
-end
-
-if not policyID then
- local request_body = ngx.var.request_body
- local postData = cjson.decode(request_body)
-
- if not request_body then
- -- ERRORCODE.PARAMETER_NONE
- local info = ERRORINFO.PARAMETER_NONE
- local desc = 'request_body or post data to get policyID'
- local response = doresp(info, desc)
- dolog(info, desc)
- ngx.say(response)
- return
- end
-
- if not postData then
- -- ERRORCODE.PARAMETER_ERROR
- local info = ERRORINFO.PARAMETER_ERROR
- local desc = 'postData is not a json string'
- local response = doresp(info, desc)
- dolog(info, desc)
- ngx.say(response)
- return
- end
-
- policyID = postData.policyid
-
- if not policyID then
- local info = ERRORINFO.PARAMETER_ERROR
- local desc = "policyID is needed"
- local response = doresp(info, desc)
- dolog(info, desc)
- ngx.say(response)
- return
- end
-
- policyID = tonumber(postData.policyid)
-
- if not policyID or policyID < 0 then
- local info = ERRORINFO.PARAMETER_TYPE_ERROR
- local desc = "policyID should be a positive Integer"
- local response = doresp(info, desc)
- dolog(info, desc)
- ngx.say(response)
- return
- end
-end
-
-
-local red = redisModule:new(redisConf)
-local ok, err = red:connectdb()
-if not ok then
- local errinfo = ERRORINFO.REDIS_CONNECT_ERROR
- local response = doresp(errinfo, err)
- dolog(errinfo, err)
- ngx.say(response)
- return
-end
-
-local pfunc = function()
- local policyMod = policyModule:new(red.redis, policyLib)
- return policyMod:get(policyID)
-end
-
-local status, info = xpcall(pfunc, handler)
-if not status then
- local errinfo = info[1]
- local errstack = info[2]
- local err, desc = errinfo[1], errinfo[2]
- local response = doresp(err, desc)
- dolog(err, desc, nil, errstack)
- ngx.say(response)
- return
-end
-
-local divtype = info.divtype
-local divdata = info.divdata
-if divtype == ngx.null or
- divdata == ngx.null then
- local err = ERRORINFO.POLICY_BLANK_ERROR
- local desc = 'policy NO.'..policyID
- local response = doresp(err, desc)
- dolog(err, desc)
- ngx.say(response)
- return
-end
-
-if not divtypes[divtype] then
- -- unsupported divtype
-end
-
-local pfunc = function()
- local divModulename = table.concat({'abtesting', 'diversion', divtype}, '.')
- local divDataKey = table.concat({policyLib, policyID, fields.divdata}, ':')
- local userInfoModulename= table.concat({'abtesting', 'userinfo', divtypes[divtype]}, '.')
-
- local runtimeMod = runtimeModule:new(red.redis, runtimeLib)
- return runtimeMod:set(domainName, divModulename, divDataKey, userInfoModulename)
-end
-
-local status, info = xpcall(pfunc, handler)
-if not status then
- local errinfo = info[1]
- local errstack = info[2]
- local err, desc = errinfo[1], errinfo[2]
- local response = doresp(err, desc)
- dolog(err, desc, nil, errstack)
- ngx.say(response)
- return
-end
-
-local response = doresp(ERRORINFO.SUCCESS)
-ngx.say(response)
diff --git a/diversion/diversion.lua b/diversion/diversion.lua
index 4ead4db..f1ac6fe 100644
--- a/diversion/diversion.lua
+++ b/diversion/diversion.lua
@@ -1,255 +1,341 @@
-local runtimeModule = require('abtesting.adapter.runtime')
+local runtimeModule = require('abtesting.adapter.runtimegroup')
local redisModule = require('abtesting.utils.redis')
local systemConf = require('abtesting.utils.init')
+local utils = require('abtesting.utils.utils')
+local logmod = require("abtesting.utils.log")
+local cache = require('abtesting.utils.cache')
local handler = require('abtesting.error.handler').handler
local ERRORINFO = require('abtesting.error.errcode').info
local cjson = require('cjson.safe')
-local utils = require('abtesting.utils.utils')
local resty_lock = require("resty.lock")
+local semaphore = require("abtesting.utils.sema")
+
+local dolog = utils.dolog
+local doerror = utils.doerror
local redisConf = systemConf.redisConf
local prefixConf = systemConf.prefixConf
local divConf = systemConf.divConf
-local cacheConf = systemConf.cacheConf
-
-local runtimeInfoLib = prefixConf.runtimeInfoPrefix
-local domainname = prefixConf.domainname
-
-local shdict_expire = divConf.shdict_expire or 60
-local default_backend = divConf.default_backend
-
-local cache_expire = cacheConf.timeout or 0.001
-local rt_cache_lock = cacheConf.runtimeInfoLock
+local indices = systemConf.indices
+local fields = systemConf.fields
+local runtimeLib = prefixConf.runtimeInfoPrefix
+local redirectInfo = 'proxypass to upstream http://'
-local dolog = utils.dolog
+local sema = semaphore.sema
+local upsSema = semaphore.upsSema
-local sysConfig = ngx.shared.sysConfig
-local kv_upstream = ngx.shared.kv_upstream
+local upstream = nil
local getRewriteInfo = function()
- return 'redirect to upstream http://'..ngx.var.backend
+ return redirectInfo..ngx.var.backend
end
-local doredirect = function()
+local doredirect = function(info)
local ok = ERRORINFO.SUCCESS
- local err = 'redirect to upstream http://'..ngx.var.backend
- dolog(ok, err)
+ local err = redirectInfo..ngx.var.backend
+ return dolog(ok, err, info)
end
-local isNULL = function(v)
- return not v or v == ngx.null
+local setKeepalive = function(red)
+ local ok, err = red:keepalivedb()
+ if not ok then
+ local errinfo = ERRORINFO.REDIS_KEEPALIVE_ERROR
+ local errdesc = err
+ dolog(errinfo, errdesc)
+ return
+ end
end
-local areNULL = function(...)
- local t = {...}
- if not next(t) then
- return true
- end
- for k, v in pairs(t) do
- if isNULL(v) then
- return true
- end
+local getHost = function()
+ local host = ngx.req.get_headers()['Host']
+ if not host then return nil end
+ local hostkey = ngx.var.hostkey
+ if hostkey then
+ return hostkey
+ else
+ --location 中不配置hostkey时
+ return host
end
- return false
end
-local isSwitchOff = function(...)
- local t = {...}
- if not next(t) then
- return true
- end
- for k, v in pairs(t) do
- if v == -1 then
- return true
- end
- end
- return false
+local getRuntime = function(database, hostname)
+ local runtimeMod = runtimeModule:new(database, runtimeLib)
+ return runtimeMod:get(hostname)
end
-local red
-local setKeepalive = function(red)
- local ok, err = red:keepalivedb()
+local getUserInfo = function(runtime)
+ local userInfoModname = runtime[fields.userInfoModulename]
+ local userInfoMod = require(userInfoModname)
+ local userInfo = userInfoMod:get()
+ return userInfo
+end
+
+local getUpstream = function(runtime, database, userInfo)
+ local divModname = runtime[fields.divModulename]
+ local policy = runtime[fields.divDataKey]
+ local divMod = require(divModname)
+ local divModule = divMod:new(database, policy)
+ local upstream = divModule:getUpstream(userInfo)
+
+ return upstream
+end
+
+local connectdb = function(red, redisConf)
+ if not red then
+ red = redisModule:new(redisConf)
+ end
+ local ok, err = red:connectdb()
if not ok then
- local errinfo = ERRORINFO.REDIS_KEEPALIVE_ERROR
- local errdesc = err
- dolog(errinfo, errdesc)
- return
+ local info = ERRORINFO.REDIS_CONNECT_ERROR
+ dolog(info, err)
+ return false, err
end
+
+ return ok, red
+end
+
+local hostname = getHost()
+if not hostname then
+ local info = ERRORINFO.ARG_BLANK_ERROR
+ local desc = 'cannot get [Host] from req headers'
+ dolog(info, desc, getRewriteInfo())
+ return nil
end
---====================================================
---获取当前domain的运行时
--- 分流模块名 divModulename
--- 分流策略库名 divDataKey
--- 用户特征提取模块名 userInfoModulename
-
-local k_divModname = runtimeInfoLib .. ':' .. domainname .. 'divModulename'
-local k_divData = runtimeInfoLib .. ':' .. domainname .. 'divDataKey'
-local k_userinfoModname = runtimeInfoLib .. ':' .. domainname .. 'userInfoModulename'
-local divModule, divPolicy, userInfoModname
-
-divModname = sysConfig:get(k_divModname)
-divPolicy = sysConfig:get(k_divData)
-userInfoModname = sysConfig:get(k_userinfoModname)
-
---step 1: read from cache
-if areNULL(divModname, divPolicy, userInfoModname) then
--- setp 2: acquire the lock
- local opts = {["timeout"] = tonumber(cache_expire)}
- local lock = resty_lock:new(rt_cache_lock, opts)
- local elapsed, err = lock:lock(userInfo)
- if not elapsed then
+local log = logmod:new(hostname)
+
+local red = redisModule:new(redisConf)
+
+-- getRuntimeInfo from cache or db
+local pfunc = function()
+ local runtimeCache = cache:new(ngx.var.sysConfig)
+
+ --step 1: read frome cache, but error
+ local divsteps = runtimeCache:getSteps(hostname)
+ if not divsteps then
+ -- continue, then fetch from db
+ elseif divsteps < 1 then
+ -- divsteps = 0, div switch off, goto default upstream
+ return false, 'divsteps < 1, div switchoff'
+ else
+ -- divsteps fetched from cache, then get Runtime From Cache
+ local ok, runtimegroup = runtimeCache:getRuntime(hostname, divsteps)
+ if ok then
+ return true, divsteps, runtimegroup
+ -- else fetch from db
+ end
+ end
+
+ --step 2: acquire the lock
+ local sem, err = sema:wait(0.01)
+ if not sem then
-- lock failed acquired
- -- but go on. This action just set a fence for all but this request
+ -- but go on. This action just sets a fence
end
-
+
-- setp 3: read from cache again
- divModname = sysConfig:get(k_divModname)
- divPolicy = sysConfig:get(k_divData)
- userInfoModname = sysConfig:get(k_userinfoModname)
-
- if areNULL(divModname, divPolicy, userInfoModname) then
- -- step 4: fetch from redis
- if not red then
- red = redisModule:new(redisConf)
- local ok, err = red:connectdb()
- if not ok then
- local errinfo = ERRORINFO.REDIS_CONNECT_ERROR
- dolog(errinfo, err, getRewriteInfo())
- local ok, err = lock:unlock()
- return
- end
+ local divsteps = runtimeCache:getSteps(hostname)
+ if not divsteps then
+ -- continue, then fetch from db
+ elseif divsteps < 1 then
+ -- divsteps = 0, div switch off, goto default upstream
+ if sem then sema:post(1) end
+ return false, 'divsteps < 1, div switchoff'
+ else
+ -- divsteps fetched from cache, then get Runtime From Cache
+ local ok, runtimegroup = runtimeCache:getRuntime(hostname, divsteps)
+ if ok then
+ if sem then sema:post(1) end
+ return true, divsteps, runtimegroup
+ -- else fetch from db
end
-
- local pfunc = function()
- local runtimeMod = runtimeModule:new(red.redis, runtimeInfoLib)
- local runtimeInfo = runtimeMod:get(domainname)
- return runtimeInfo
- end
- local status, info = xpcall(pfunc, handler)
- if not status then
- local errinfo = info[1]
- local errstack = info[2]
- local err, desc = errinfo[1], errinfo[2]
- dolog(err, desc, getRewriteInfo(), errstack)
- local ok, err = lock:unlock()
- return
- end
-
- divModname = info[1]
- divPolicy = info[2]
- userInfoModname = info[3]
-
- if areNULL(divModname, divPolicy, userInfoModname) then
- local errinfo = ERRORINFO.RUNTIME_BLANK_ERROR
- local errdesc = 'runtimeInfo blank'
-
- sysConfig:set(k_divModname, -1, shdict_expire)
- sysConfig:set(k_divData, -1, shdict_expire)
- sysConfig:set(k_userinfoModname, -1, shdict_expire)
- local ok, err = lock:unlock()
-
- if red then setKeepalive(red) end
- dolog(errinfo, errdesc, getRewriteInfo())
- return
- else
- sysConfig:set(k_divModname, divModname, shdict_expire)
- sysConfig:set(k_divData, divPolicy, shdict_expire)
- sysConfig:set(k_userinfoModname, userInfoModname, shdict_expire)
- local ok, err = lock:unlock()
- end
end
-elseif isSwitchOff(divModname, divPolicy, userInfoModname) then
- -- switchoff, so goto default upstream
- doredirect()
- return
-else
- -- maybe userful
-end
+ -- step 4: fetch from redis
+ local ok, db = connectdb(red, redisConf)
+ if not ok then
+ if sem then sema:post(1) end
+ return ok, db
+ end
---====================================================
---准备工作:
--- 分流模块 divModule
--- 用户特征提取模块 userInfoModule
---获取用户信息:
--- 用户信息 userInfo
-local userInfoMod
-local diversionMod
-local userInfo
+ local database = db.redis
+ local runtimeInfo = getRuntime(database, hostname)
-local pfunc = function()
- userInfoMod = require(userInfoModname)
- diversionMod = require(divModname)
- userInfo = userInfoMod:get()
-end
-local ok, info = xpcall(pfunc, handler)
-if not ok then
- local errinfo = info[1]
- local errstack = info[2]
- local err, desc = errinfo[1], errinfo[2]
- dolog(err, desc, getRewriteInfo(), errstack)
+ local divsteps = runtimeInfo.divsteps
+ local runtimegroup = runtimeInfo.runtimegroup
+
+ runtimeCache:setRuntime(hostname, divsteps, runtimegroup)
if red then setKeepalive(red) end
- return
+
+ if sem then sema:post(1) end
+ return true, divsteps, runtimegroup
end
-if not userInfo then
- local errinfo = ERRORINFO.USERINFO_BLANK_ERROR
- local errdesc = userInfoModulename
- dolog(errinfo, errdesc, getRewriteInfo())
- if red then setKeepalive(red) end
- return
+local ok, status, steps, runtimeInfo = xpcall(pfunc, handler)
+if not ok then
+ -- execute error, the type of status is table now
+ log:errlog("getruntime\t", "error\t")
+ return doerror(status, getRewriteInfo())
+else
+ local info = 'getRuntimeInfo error: '
+ if not status or not steps or steps < 1 then
+ if not status then
+ local reason = steps
+ if reason then
+ info = info .. reason
+ end
+ elseif not steps then
+ info = info .. 'no divsteps, div switch OFF'
+ elseif steps < 1 then
+ info = info .. 'divsteps < 1, div switch OFF'
+ end
+ return log:info(doredirect(info))
+ else
+ log:debug('divstep = ', steps,
+ '\truntimeinfo = ', cjson.encode(runtimeInfo))
+ end
end
-------------------分流准备工作结束--------------------
---====================================================
-local upstream, err = kv_upstream:get(userInfo)
-if not upstream then
+local divsteps = steps
+local runtimegroup = runtimeInfo
- if not red then
- red = redisModule:new(redisConf)
- local ok, err = red:connectdb()
- if not ok then
- local errinfo = ERRORINFO.REDIS_CONNECT_ERROR
- dolog(errinfo, err, getRewriteInfo())
- return
+local pfunc = function()
+
+ local upstreamCache = cache:new(ngx.var.kv_upstream)
+
+ local usertable = {}
+ for i = 1, divsteps do
+ local idx = indices[i]
+ local runtime = runtimegroup[idx]
+ local info = getUserInfo(runtime)
+
+ if info and info ~= '' then
+ usertable[idx] = info
end
end
-
- local pfunc = function()
- local divModule = diversionMod:new(red.redis, divPolicy)
- local upstream = divModule:getUpstream(userInfo)
- return upstream
+
+ log:debug('userinfo\t', cjson.encode(usertable))
+
+
+-- usertable is empty, it seems that will never happen
+-- if not next(usertable) then
+-- return nil
+-- end
+
+ --step 1: read frome cache, but error
+ local upstable = upstreamCache:getUpstream(divsteps, usertable)
+ log:debug('first fetch: upstable in cache\t', cjson.encode(upstable))
+ for i = 1, divsteps do
+ local idx = indices[i]
+ local ups = upstable[idx]
+ if ups == -1 then
+ if i == divsteps then
+ local info = "usertable has no upstream in cache 1, \
+ proxypass to default upstream"
+ log:info(info)
+ return nil, info
+ end
+ -- continue
+ elseif ups == nil then
+ -- why to break
+ -- the reason is that maybe some userinfo is empty
+ -- 举例子,用户请求
+ -- location/div -H 'X-Log-Uid:39' -H 'X-Real-IP:192.168.1.1'
+ -- 分流后缓存中 39->-1, 192.168.1.1-> beta2
+ -- 下一请求:
+ -- location/div?city=BJ -H 'X-Log-Uid:39' -H 'X-Real-IP:192.168.1.1'
+ -- 该请求应该是 39-> -1, BJ->beta1, 192.168.1.1->beta2,
+ -- 然而cache中是 39->-1, 192.168.1.1->beta2,
+ -- 如果此分支不break的话,将会分流到beta2上,这是错误的。
+
+ break
+ else
+ local info = "get upstream ["..ups.."] according to ["
+ ..idx.."] userinfo ["..usertable[idx].."] in cache 1"
+ log:info(info)
+ return ups, info
+ end
end
- local status, backend = xpcall(pfunc, handler)
- if not status then
- local info = backend
- local errinfo = info[1]
- local errstack = info[2]
- local err, desc = errinfo[1], errinfo[2]
- dolog(err, desc, getRewriteInfo(), errstack)
- return
+
+ --step 2: acquire the lock
+ local sem, err = upsSema:wait(0.01)
+ if not sem then
+ -- lock failed acquired
+ -- but go on. This action just set a fence for all but this request
+ end
+
+ -- setp 3: read from cache again
+ local upstable = upstreamCache:getUpstream(divsteps, usertable)
+ log:debug('second fetch: upstable in cache\t', cjson.encode(upstable))
+ for i = 1, divsteps do
+ local idx = indices[i]
+ local ups = upstable[idx]
+ if ups == -1 then
+ -- continue
+ if i == divsteps then
+ local info = "usertable has no upstream in cache 2, \
+ proxypass to default upstream"
+ return nil, info
+ end
+
+ elseif ups == nil then
+ -- do not break, may be the next one will be okay
+ break
+ else
+ if sem then upsSema:post(1) end
+ local info = "get upstream ["..ups.."] according to ["
+ ..idx.."] userinfo ["..usertable[idx].."] in cache 2"
+ return ups, info
+ end
+ end
+
+ -- step 4: fetch from redis
+ local ok, db = connectdb(red, redisConf)
+ if not ok then
+ if sem then upsSema:post(1) end
+ return nil, db
end
-
- upstream = backend
+ local database = db.redis
+
+ for i = 1, divsteps do
+ local idx = indices[i]
+ local runtime = runtimegroup[idx]
+ local info = usertable[idx]
+
+ if info then
+ local upstream = getUpstream(runtime, database, info)
+ if not upstream then
+ upstreamCache:setUpstream(info, -1)
+ log:debug('fetch userinfo [', info, '] from db, get [nil]')
+ else
+ if sem then upsSema:post(1) end
+ if red then setKeepalive(red) end
+
+ upstreamCache:setUpstream(info, upstream)
+ log:debug('fetch userinfo [', info, '] from db, get [', upstream, ']')
+
+ local info = "get upstream ["..upstream.."] according to ["
+ ..idx.."] userinfo ["..usertable[idx].."] in db"
+ return upstream, info
+ end
+ end
+ end
+
+ if sem then upsSema:post(1) end
+ if red then setKeepalive(red) end
+ return nil, 'the req has no target upstream'
end
-if upstream then
- ngx.var.backend = upstream
+local status, info, desc = xpcall(pfunc, handler)
+if not status then
+ doerror(info)
else
- upstream = default_backend
+ upstream = info
end
-kv_upstream:set(userInfo, upstream, shdict_expire)
-doredirect()
---------------------分流结果结束----------------------
---====================================================
-
---====================================================
----------------------后续处理-------------------------
----如果本次请求使用过redis,设置redis对象的keepalive---
-------------------------------------------------------
-if red then
- setKeepalive(red)
+if upstream then
+ ngx.var.backend = upstream
end
+local info = doredirect(desc)
+log:errlog(info)
diff --git "a/doc/ab\345\210\206\346\265\201\347\255\226\347\225\245.md" "b/doc/ab\345\210\206\346\265\201\347\255\226\347\225\245.md"
new file mode 100644
index 0000000..a2479b1
--- /dev/null
+++ "b/doc/ab\345\210\206\346\265\201\347\255\226\347\225\245.md"
@@ -0,0 +1,128 @@
+ab分流策略格式
+======================
+
+* 分流策略 policy
+* 分流策略组 policygroup
+
+分流策略policy
+--------------------------
+
+```bash
+{
+ "divtype":"分流类型",
+ "divdata":[
+ {规则一},
+ {规则二},
+ {规则三},
+ ...
+ ]
+}
+```
+
+* ab 灰度系统目前支持的策略有ip段分流、用户uid段分流、uid尾数分流、uid白名单分流
+* 可以灵活添加新的分流方式
+
+```bash
+#iprange分流,其中start和end为ip的整型表示。
+{
+ "divtype":"iprange",
+ "divdata":[
+ {"range":{"start":1111, "end":2222}, "upstream":"beta1"},
+ {"range":{"start":3333, "end":4444}, "upstream":"beta2"},
+ {"range":{"start":7777, "end":8888}, "upstream":"beta3"}
+ ]
+}
+```
+
+```bash
+#uid段分流
+{
+ "divtype": "uidrange",
+ "divdata": [
+ {"range":{"start":1111, "end":2222}, "upstream":"beta1"},
+ {"range":{"start":3333, "end":4444}, "upstream":"beta2"}
+ ]
+}
+```
+
+```bash
+#uid尾数分流
+{
+ "divtype": "uidsuffix",
+ "divdata": [
+ {"suffix":1, "upstream":"beta1"},
+ {"suffix":3, "upstream":"beta2"},
+ {"suffix":5, "upstream":"beta1"},
+ {"suffix":0, "upstream":"beta3"}
+ ]
+}
+```
+
+```bash
+#uid白名单分流
+{
+ "divtype": "uidappoint",
+ "divdata": [
+ {"uidset":[1234,5124,653], "upstream":"beta1"},
+ {"uidset":[3214,652,145], "upstream":"beta2"}
+ ]
+}
+```
+* 当向系统添加分流策略时,需要将策略数据转为json类型字符串,以POST方式访问添加策略接口
+* http://www.bejson.com/jsoneditoronline/ 可以将上述策略转换为字符串,用以通过post方式向系统添加策略
+* 以上四条策略的字符串格式分别为:
+ * {"divtype":"iprange","divdata":[{"range":{"start":1111,"end":2222},"upstream":"beta1"},{"range":{"start":3333,"end":4444},"upstream":"beta2"},{"range":{"start":7777,"end":8888},"upstream":"beta3"}]}
+ * {"divtype":"uidrange","divdata":[{"range":{"start":1111,"end":2222},"upstream":"beta1"},{"range":{"start":3333,"end":4444},"upstream":"beta2"}]}
+ * {"divtype":"uidsuffix","divdata":[{"suffix":1,"upstream":"beta1"},{"suffix":3,"upstream":"beta2"},{"suffix":5,"upstream":"beta1"},{"suffix":0,"upstream":"beta3"}]}
+ * {"divtype":"uidappoint","divdata":[{"uidset":[1234,5124,653],"upstream":"beta1"},{"uidset":[3214,652,145],"upstream":"beta2"}]}
+
+
+分流策略组policygroup
+--------------------------
+
+* 分流策略组中会有多个策略
+* 优先级由数字表示,从1开始,级别为1的策略优先级最高
+* 分流策略组格式为:
+
+```bash
+{
+ "1":{
+ "divtype":"分流类型",
+ "divdata":[
+ {规则一},
+ {规则二},
+ ...
+ ]
+ },
+ "2":{
+
+ },
+ ...
+}
+```
+* 以下是一个包含两级分流策略,第一级为uid白名单分流策略,第二级为ip段分流
+
+```bash
+{
+
+ "1":{
+ "divtype": "uidappoint",
+ "divdata": [
+ {"uidset":[1234,5124,653], "upstream":"beta1"},
+ {"uidset":[3214,652,145], "upstream":"beta2"}
+ ]
+ },
+ "2":{
+ "divtype":"iprange",
+ "divdata":[
+ {"range":{"start":1111, "end":2222}, "upstream":"beta1"},
+ {"range":{"start":3333, "end":4444}, "upstream":"beta2"},
+ {"range":{"start":7777, "end":8888}, "upstream":"beta3"}
+ ]
+ }
+}
+```
+* 该分流策略组的字符串形式为:
+ * {"1":{"divtype":"uidappoint","divdata":[{"uidset":[1234,5124,653],"upstream":"beta1"},{"uidset":[3214,652,145],"upstream":"beta2"}]},"2":{"divtype":"iprange","divdata":[{"range":{"start":1111,"end":2222},"upstream":"beta1"},{"range":{"start":3333,"end":4444},"upstream":"beta2"},{"range":{"start":7777,"end":8888},"upstream":"beta3"}]}}
+
+
diff --git "a/doc/ab\345\212\237\350\203\275\346\216\245\345\217\243\344\275\277\347\224\250\344\273\213\347\273\215.md" "b/doc/ab\345\212\237\350\203\275\346\216\245\345\217\243\344\275\277\347\224\250\344\273\213\347\273\215.md"
new file mode 100644
index 0000000..a9a99e4
--- /dev/null
+++ "b/doc/ab\345\212\237\350\203\275\346\216\245\345\217\243\344\275\277\347\224\250\344\273\213\347\273\215.md"
@@ -0,0 +1,181 @@
+ab功能接口介绍
+===================
+
+ab管理接口
+------------------
+
+```bash
+#策略管理
+* /ab_admin?action=policy_check
+* /ab_admin?action=policy_set
+* /ab_admin?action=policy_get
+* /ab_admin?action=policy_del
+
+#策略组管理(用于多级分流)
+* /ab_admin?action=policygroup_check
+* /ab_admin?action=policygroup_set
+* /ab_admin?action=policygroup_get
+* /ab_admin?action=policygroup_del
+
+#运行时信息设置(其中runtime_set接受policyid和policygroupid参数,分别用于单级分流和多级分流)
+* /ab_admin?action=runtime_get
+* /ab_admin?action=runtime_set
+* /ab_admin?action=runtime_del
+```
+* 1.检查策略是否合法
+ * http://localhost:port/ab_admin?action=policy_check -d '{"divtype":"uidsuffix","divdata":[{"suffix":"1","upstream":"beta1"},{"suffix":"3","upstream":"beta2"},{"suffix":"5","upstream":"beta1"},{"suffix":"0","upstream":"beta3"}]}'
+ * 接口说明:
+ * action: 代表要执行的操作,检查策略接口为policy_check
+ * 仅接受POST方法,POST数据为待检查策略的json字符串
+ * 返回值:{"code":200,"desc":"success "},系统中如果返回非200的code码,就认为是发生错误,desc为错误信息。
+ * 错误返回值:{"code":50102,"desc":"parameter error for postData is not a json string"} 如果出错,返回错误码与对应错误信息,反馈给用户,其他接口同样。
+
+
+* 2.向系统添加策略
+ * http://localhost:port/ab_admin?action=policy_set -d '{"divtype":"uidsuffix","divdata":[{"suffix":"1","upstream":"beta1"},{"suffix":"3","upstream":"beta2"},{"suffix":"5","upstream":"beta1"},{"suffix":"0","upstream":"beta3"}]}'`
+
+ * 接口说明:
+ * action: 代表要执行的操作
+ * 仅接受POST方法,POST数据为待检查策略的json字符串
+ * 返回值:{"code":200,"desc":"success the id of new policy is 20"},策略添加成功,返回策略号policyid,样例中policyid为20
+
+* 3.从系统读取策略
+ * http://localhost:port/ab_admin?action=policy_get&policyid=20
+
+ * 接口说明:
+ * 参数:action: 代表要执行的操作
+ * 参数:policyid: 获取第policyid号策略
+ * 返回值:{"desc":"success ","code":200,"data":{"divdata":["1","beta1","3","beta2","5","beta1","0","beta3"],"divtype":"uidsuffix"}} 返回值中data部分是读取的策略数据,json格式。
+
+* 4.从系统删除策略
+ * http://localhost:port/ab_admin?action=policy_del&policyid=20
+
+ * 接口说明:
+ * 参数:action: 代表要执行的操作
+ * 参数:policyid: 删除第policyid号策略
+ * 返回值:{"code":200,"desc":"success "}
+
+* 5.检查策略组是否合法
+ * http://localhost:port/ab_admin?action=policygroup_check -d '{"1":{"divtype":"uidappoint","divdata":[{"uidset":[1234,5124,653],"upstream":"beta1"},{"uidset":[3214,652,145],"upstream":"beta2"}]},"2":{"divtype":"iprange","divdata":[{"range":{"start":1111,"end":2222},"upstream":"beta1"},{"range":{"start":3333,"end":4444},"upstream":"beta2"},{"range":{"start":7777,"end":8888},"upstream":"beta3"}]}}
+
+ * 接口说明:
+ * action: 代表要执行的操作,检查策略接口为policygroup_check
+ * 仅接受POST方法,POST数据为待检查策略的json字符串
+ * 返回值:{"code":200,"desc":"success "},系统中如果返回非200的code码,就认为是发生错误,desc为错误信息。
+ * 错误返回值:{"code":50102,"desc":"parameter error for postData is not a json string"} 如果出错,返回错误码与对应错误信息,反馈给用户,其他接口同样。
+
+
+* 6.向系统添加策略组
+ * http://localhost:port/ab_admin?action=policygroup_set -d '{"1":{"divtype":"uidappoint","divdata":[{"uidset":[1234,5124,653],"upstream":"beta1"},{"uidset":[3214,652,145],"upstream":"beta2"}]},"2":{"divtype":"iprange","divdata":[{"range":{"start":1111,"end":2222},"upstream":"beta1"},{"range":{"start":3333,"end":4444},"upstream":"beta2"},{"range":{"start":7777,"end":8888},"upstream":"beta3"}]}}
+
+ * 接口说明:
+ * action: 代表要执行的操作
+ * 仅接受POST方法,POST数据为待检查策略的json字符串
+ * 返回值:{"desc":"success ","code":200,"data":{"groupid":2,"group":[11,12]}},策略组添加成功,返回策略组号groupid是2,组中包括两个策略,策略id分别是11和12.
+
+* 7.从系统读取策略组
+ * http://localhost:port/ab_admin?action=policygroup_get&policygroupid=2
+
+ * 接口说明:
+ * 参数:action: 代表要执行的操作
+ * 参数:policyid: 获取第policygroupid号策略组
+ * 返回值:{"desc":"success ","code":200,"data":{"groupid":2,"group":["11","12"]}} 返回值以json格式返回该组策略中包括哪些策略。
+
+* 8.从系统删除策略组
+ * http://localhost:port/ab_admin?action=policygroup_del&policygroupid=2
+
+ * 接口说明:
+ * 参数:action: 代表要执行的操作
+ * 参数:policyid: 删除第policygroupid号策略组
+ * 返回值:{"code":200,"desc":"success "}
+
+* 9.设置***策略***为系统的运行时策略,进行单级分流
+ * http://localhost:port/ab_admin?action=runtime_set&policyid=22&hostname=api.weibo.cn
+
+ * 接口说明:
+ * 参数:action: 代表要执行的操作
+ * 参数:policyid: 设置第policyid号策略为运行时策略
+ * 参数:hostname:非常重要,向server api.weibo.cn绑定运行时信息,或向location /abc @server api.weibo.cn绑定运行时信息
+ * 返回值:{"code":200,"desc":"success "}
+ * 注意:设置运行时信息的动作会导致原来数据库中的运行时信息删除,不论本次设置是否成功
+
+* 10.设置***策略组***为系统的运行时策略,进行多级分流
+ * http://localhost:port/ab_admin?action=runtime_set&policygroupid=4&hostname=api.weibo.cn
+
+ * 接口说明:
+ * 参数:action: 代表要执行的操作
+ * 参数:policygroupid: 设置第policygroupid号策略组 为 运行时策略
+ * 参数:hostname: 为host api.weibo.cn设置运行时策略
+ * 返回值:{"code":200,"desc":"success "}
+ * 返回值:若发生错误,则有相关提示,比如某策略不存在。
+
+ * 请注意:将 策略 或者 策略组 设置为运行时策略的接口是一样的,区别的方式在于参数是policyid还是policygroupid,所以要注意不要写错。
+ * 请注意:设置运行时信息的动作会导致原来数据库中的运行时信息删除,不论本次设置是否成功
+
+
+* 11.获取系统运行时信息
+ * http://localhost:port/ab_admin?action=runtime_get&hostname=api.weibo.cn
+
+ * 接口说明:
+ * 参数:action: 代表要执行的操作,获取系统运行时信息runtime_get
+ * 参数:hostname: 获取hostname主机的运行时信息
+ * 系统未设置运行时信息时,返回值{"desc":"success ","code":200,"data":{"divsteps":0,"runtimegroup":{}}}
+ * 系统设置运行时信息后,举例为:
+
+```bash
+ {
+ "desc": "success ",
+ "code": 200,
+ "data": {
+ "divsteps": 2,
+ "runtimegroup": {
+ "second": {
+ "divModulename": "abtesting.diversion.iprange",
+ "divDataKey": "ab:test:policies:16:divdata",
+ "userInfoModulename": "abtesting.userinfo.ipParser"
+ },
+ "first": {
+ "divModulename": "abtesting.diversion.uidappoint",
+ "divDataKey": "ab:test:policies:15:divdata",
+ "userInfoModulename": "abtesting.userinfo.uidParser"
+ }
+ }
+ }
+ }
+ # divsteps表示几级分流
+ # runtimegroup是分流信息,以first、second等作为下标,最多十级分流
+ # divModulename为运行时的分流模块名
+ # userInfoModulename为运行时的用户信息提取模块名
+ # divDataKey为运行时的分流策略名
+```
+
+* 12.删除系统运行时信息
+ * http://localhost:port/ab_admin?action=runtime_del&hostname=api.weibo.cn
+
+ * 接口说明:
+ * 参数:action: 代表要执行的操作,删除系统运行时信息runtime_del
+ * 返回值:{"code":200,"desc":"success "}
+
+ab分流接口
+------------------
+
+* ab分流接口目前只能配置为 location /
+* 以***ab管理接口***小节中的第11条获取运行时信息为例,第一级是uidappoint白名单分流,第二级是iprange ip段分流方式
+
+* curl http://localhost:port/ -H 'Host:api.weibo.cn' -H 'X-Uid:30'
+ * HOST字段是每个合法用户请求都有的,从HTTP 请求头中获取
+ * 在匹配到virtual host和location后,分流功能通过location中设置的***hostkey***字段找到运行时信息,然后进行下一步的分流。
+ * 因此location中的***$hostkey***字段是分流的基础,这里与ab管理功能中的设置运行时信息中的hostname参数一样
+
+response格式
+------------------
+
+系统response采用json方式返回,resp包括返回码**code**、调用信息**desc**和调用结果**data**:
+
+* 操作成功
+{***"code"***:200, ***"desc"***:"success", ***"data"***:["stable","beta1","beta2","beta3","beta4","beta5"]}
+
+* 操作错误
+{***"code"***:500, ***"desc"***:"Invalid operation: get_upstream"}
+
+
diff --git "a/doc/ab\345\212\237\350\203\275\351\241\273\347\237\245.md" "b/doc/ab\345\212\237\350\203\275\351\241\273\347\237\245.md"
new file mode 100644
index 0000000..919890a
--- /dev/null
+++ "b/doc/ab\345\212\237\350\203\275\351\241\273\347\237\245.md"
@@ -0,0 +1,71 @@
+ab分流功能须知
+-------------------
+
+转发分流是灰度系统的主要功能,目前 ABTestingGateway 支持 `ip段分流(iprange)`、`uid用户段分流(uidrange)`、`uid尾数分流(uidsuffix)` 和 `指定特殊uid分流(uidappoint)` 四种方式。
+
+ABTestingGateway 依据系统中配置的 `运行时信息runtimeInfo` 进行分流工作;通过将 runtimeInfo 设置为不同的分流策略,实现运行时分流策略的动态更新,达到动态调度的目的。
+
+对于ab功能而言,步骤是以下三步:
+
+1. 向系统添加策略,将策略写入策略数据库中
+1. 为具体的server设置运行时信息,将某个分流策略设置为运行时策略
+1. 之后可以进行分流操作
+
+### 1. 向系统添加策略 ###
+向系统中添加分流策略的过程,本质上是将分流策略写入到系统的redis中,这个过程与具体哪个server没有关系,只是将分流策略以id为key存入redis中。本系统采用***ab:test:policies***为策略前缀,比如某个策略写入redis成功后,返回policyId=1, 那么在redis中,key为***ab:test:policyies:1:divtype***和***ab:test:policyies:1:divdata***将用来存储策略1的类型type和规则。
+同样的,向系统添加分流策略组,首先将策略组中的单个策略写入系统中,然后返回策略组的policyGroupId。
+
+### 2. 为具体的server设置运行时信息 ###
+将某个策略设置成server的运行时策略,最终将这个运行时信息写入到redis中。运行时信息包括三个元素,分流模块名divModuleName,分流策略名divDataKey和用户信息提取模块名userInfoModuleName;运行时信息以***ab:test:runtimeInfo***为前缀;server name为redis中key的关键部分,用于甄别不同server的运行时信息。最终redis中存储的运行时信息是
+
+```bash
+ ab:test:runtimeInfo:xxx.weibo.cn:first:divModulename
+ ab:test:runtimeInfo:xxx.weibo.cn:first:divDataKey
+ ab:test:runtimeInfo:xxx.weibo.cn:first:userInfoModulename
+
+ ab:test:runtimeInfo:xxx.weibo.cn:second:divModulename
+ ab:test:runtimeInfo:xxx.weibo.cn:second:divDataKey
+ ab:test:runtimeInfo:xxx.weibo.cn:second:userInfoModulename
+
+ # ab:test:runtimeInfo 为前缀
+ # xxx.weibo.cn 是server name
+ # first和second分别表示第一级分流和第二级分流
+ # divModulename等是运行时信息的元素
+```
+因此设置运行时信息时,server name是关键。
+运行时信息设置的接口是
+
+ /ab_admin?action=runtime_set&policyid=0&hostname=xxx.weibo.cn
+
+向hostname=xxx.weibo.cn设置运行时信息,完全是在访问runtime_set接口时的hostname参数中指定的。
+
+因此,如果引入location级别的运行时信息,我们只需要在调用runtime_set接口时指定hostname就可以。这个hostname同时在location中指定,比如对location /abc设置分流信息时,hostname指定为xxx.weibo.cn.abc,这样在对访问/abc接口的请求进行分流时,以xxx.weibo.cn.abc为key的分流信息生效(例如 ab:test:runtiemInfo:xxx.weibo.cn.abc:divModulename)。具体配置方法见下文
+
+### 3. 对用户请求进行分流 ###
+对用户请求进行分流的过程:
+
+1. 提取用户请求的HOST字段,拿到以***ab:test:runtimeInfo***和***HOST***为前缀的运行时信息的三要素
+2. 用户信息提取模块userInfoModule提取用户信息userInfo
+3. 分流模块divmodule根据分流策略divDataKey和userInfo计算得到对应的upstream,转发;如果没有对应的upstream,则转向默认upstream。
+
+* 分流三要素的用途
+
+
+* 分流过程流程图
+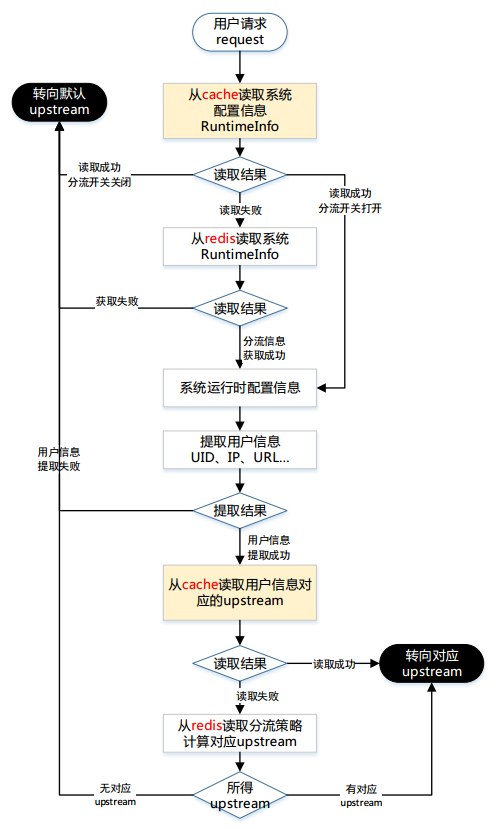
分流过程流程图